- Course
Technical Information Gathering with theHarvester
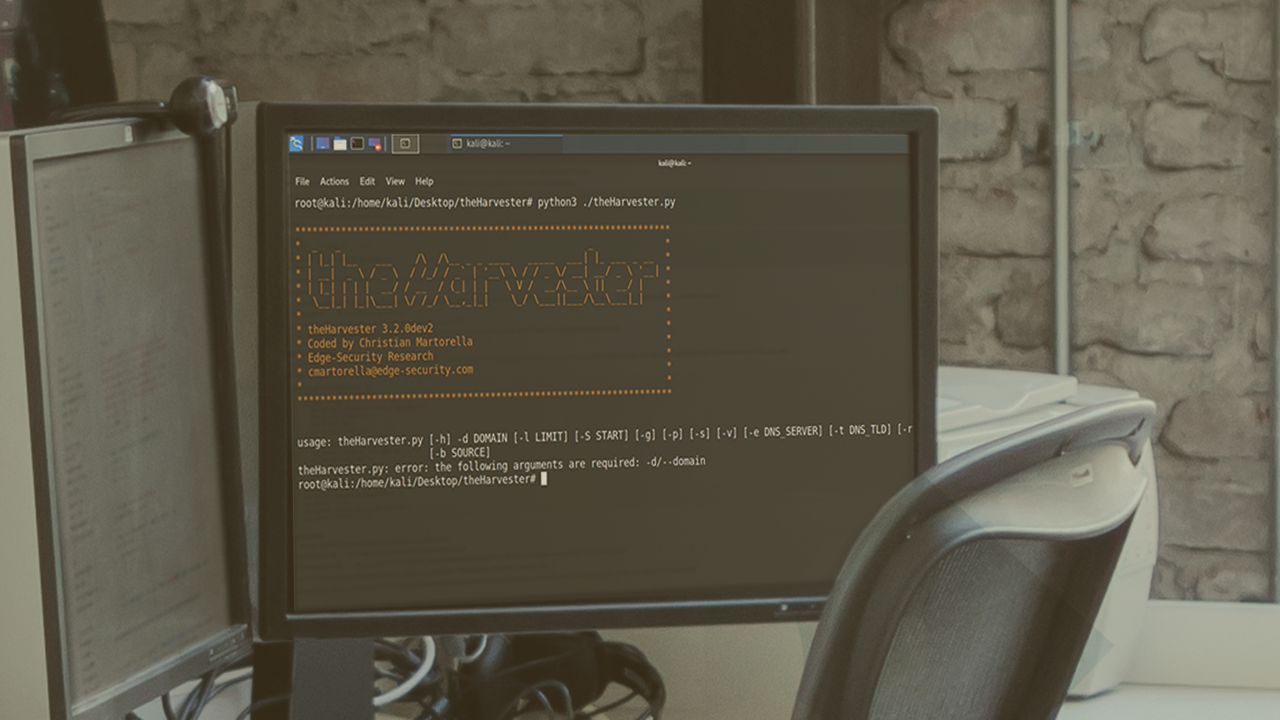
The first and most important part of a red team engagement is reconnaissance. In this course, you will learn to gather technical information such as DNS subdomains and IP addresses, as well as people information, using theHarvester.
- Course
Technical Information Gathering with theHarvester
The first and most important part of a red team engagement is reconnaissance. In this course, you will learn to gather technical information such as DNS subdomains and IP addresses, as well as people information, using theHarvester.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
The reconnaissance phase is one of the most important phases of a red team engagement. It is in this phase that you gather information about your target so you can select which machines to exploit and how to exploit them. In this course, Technical Information Gathering with theHarvester, you will cover one of the most important tools for information gathering, ttheHarvester. First, you will learn to gather DNS subdomains. Then, you will discover how to gather IP addresses from your target. Finally, you will explore how to automatically search for information regarding the people that work in your target company, including email addresses, Twitter accounts, and even LinkedIn profiles. By the end of this course, you will know four important tactics from the MITRE PRE-ATT&CK framework: Determine domain and IP Address Space (T1250), Conduct Active Scanning (T1254), Discover target logon/email address format (T1255) and Mine Social Media (T1273).

