- Course
VMware vSphere Security Design: Security Basics
Part 1 of 3 in the VMware vSphere Security Design series focuses on the essential security concepts in VMware virtualization.
- Course
VMware vSphere Security Design: Security Basics
Part 1 of 3 in the VMware vSphere Security Design series focuses on the essential security concepts in VMware virtualization.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
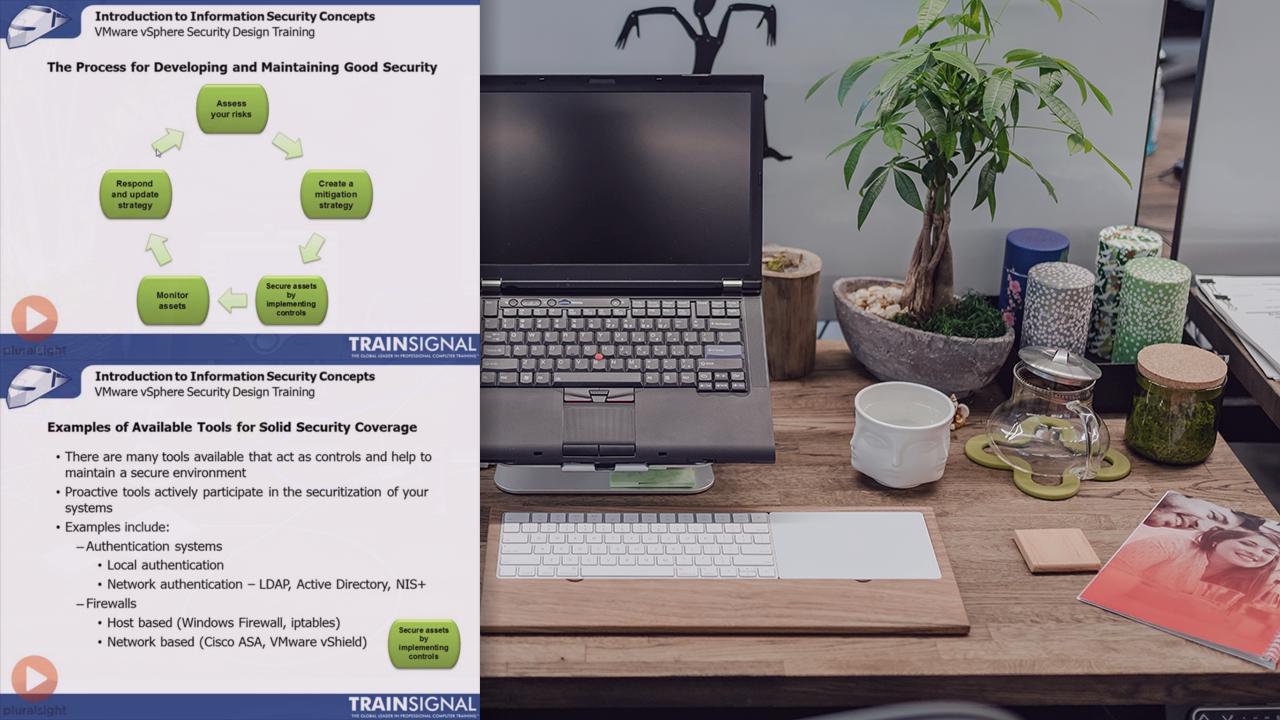
Part 1 of 3 in the VMware vSphere Security Design series focuses on the essential security concepts in VMware virtualization. The goal of this course is to take you beyond basic implementation, configuration, and administration of VMware vSphere and teach you the skills needed to properly secure a vSphere environment. You’ll learn information security and risk management concepts, how virtualization affects security, guidelines and best practices for securing a virtual environment, and securing virtual machines. This course is recommended for those who have existing VMware vSphere knowledge who want to enhance their security knowledge.

