- Course
Zero Trust Networking (ZTN): The Big Picture
Essentially, with Zero Trust Networking, the network is entirely dark to everything and everyone until the administrator turns the lights on. You will go through technologies and introduced to new networking and security architectures.
- Course
Zero Trust Networking (ZTN): The Big Picture
Essentially, with Zero Trust Networking, the network is entirely dark to everything and everyone until the administrator turns the lights on. You will go through technologies and introduced to new networking and security architectures.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
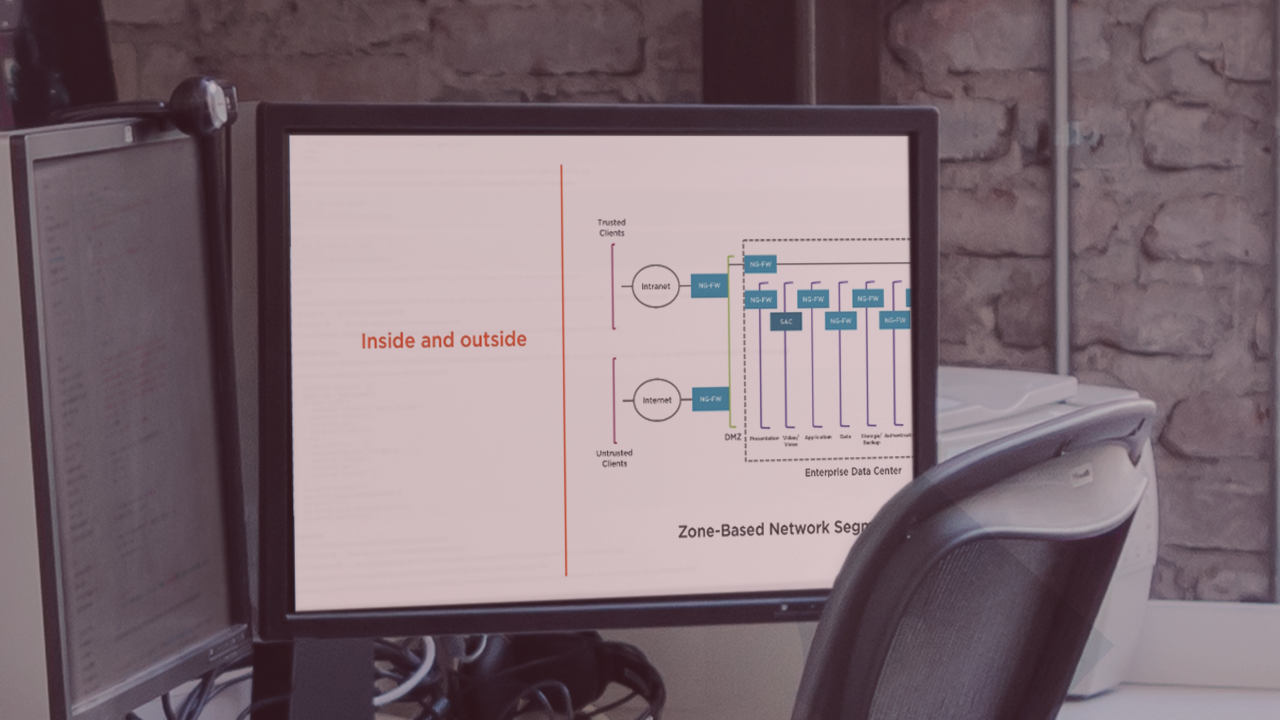
Initially, networks were designed solely for connectivity i.e to share a printer. Back 30 years ago a printer could cost the same as a house so it was pretty important to be able to share it. In this course, Zero Trust Networking (ZTN): The Big Picture, you will learn foundational knowledge and gain the ability to evolve your network to match the new digital world and combat the bad actors both internal and external to your network. First, you will learn why we need Zero Trust Networking. Next, you will discover some of the components used to create a new network and security model and a good understanding of how Zero Trust Networking works. Finally, you will explore how to two Zero Trust projects of Microsegmention and Software-defined perimeter. When you’re finished with this course, you will have the skills and knowledge of Zero Trust Networking needed to match the new digital age and combat bad actors both internal and external to your network.

