- Course
Application Analysis with Endlessh 1
In this course, you'll learn how to protect your SSH server against service flood attacks using Endlessh.
- Course
Application Analysis with Endlessh 1
In this course, you'll learn how to protect your SSH server against service flood attacks using Endlessh.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
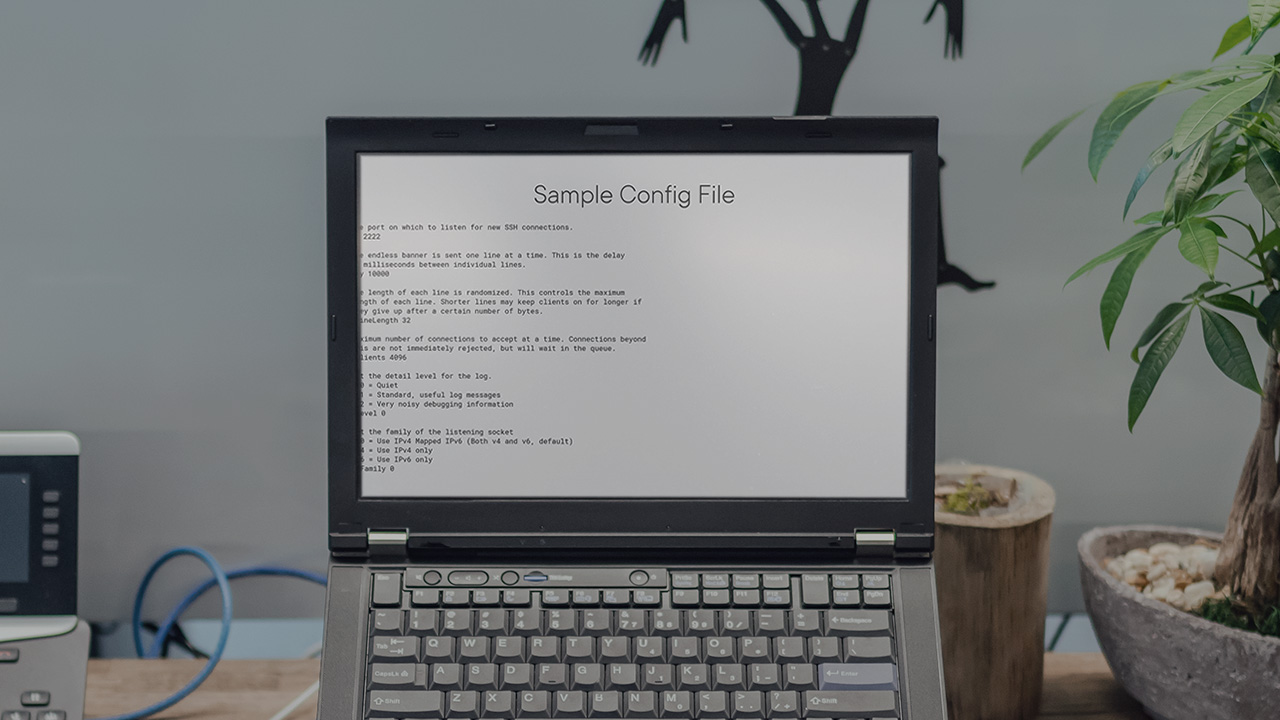
Endlessh is an effective tool that protects your SSH server from attacks by acting as a decoy and tricking the potential attackers. In this course, Application Analysis with Endlessh, you'll learn how to utilize Endlessh to protect against service exhaustion flood attacks in an enterprise environment. First, you'll demonstrate how Endlessh should be configured. Next, you'll conduct a service flood attack on an SSH server. Finally, you'll analyze how Endlessh is trapping attackers by slowly sending random SSH banners. By the end of this course, you’ll have the skills and knowledge to use these techniques of creating a decoy system using Endlessh, in order to avoid automated attacks against your SSH server.

