- Course
Understanding ASP.NET Core Security
This course has been updated to explain security in ASP.NET Core 2. ASP.NET Core security shouldn't be an afterthought when designing an application. Learn how to mitigate common attacks and implement encryption, authentication, and authorization.
- Course
Understanding ASP.NET Core Security
This course has been updated to explain security in ASP.NET Core 2. ASP.NET Core security shouldn't be an afterthought when designing an application. Learn how to mitigate common attacks and implement encryption, authentication, and authorization.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
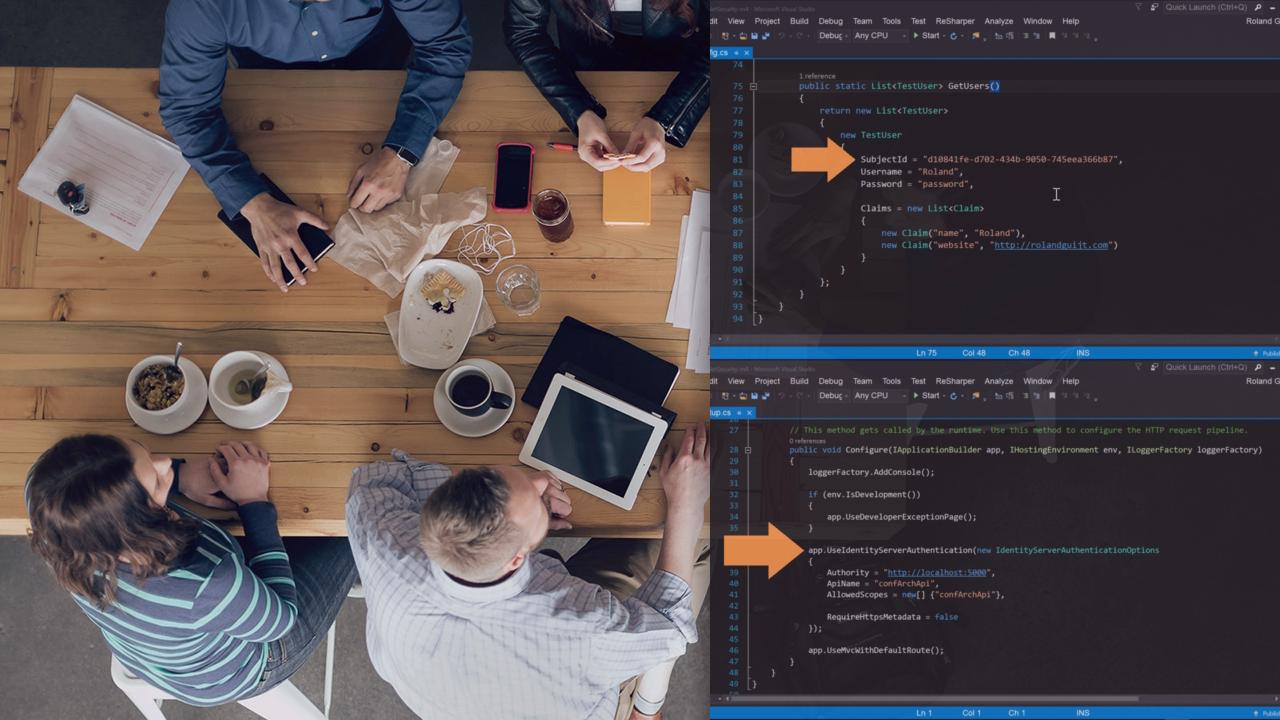
Learn how to make your ASP.NET Core app secure in this course. First you'll learn about common attacks and how to mitigate them with NWebSec. You'll learn the ins and outs of the new encryption API and how to protect secrets with the secret manager. Authentication is covered by explaining ASP.NET Core Identity as well as implementing a token service with IdentityServer. Finally you'll see that ASP.NET Core's authorization system is now policy based.

