- Course
AWS Developer: Deployment and Security
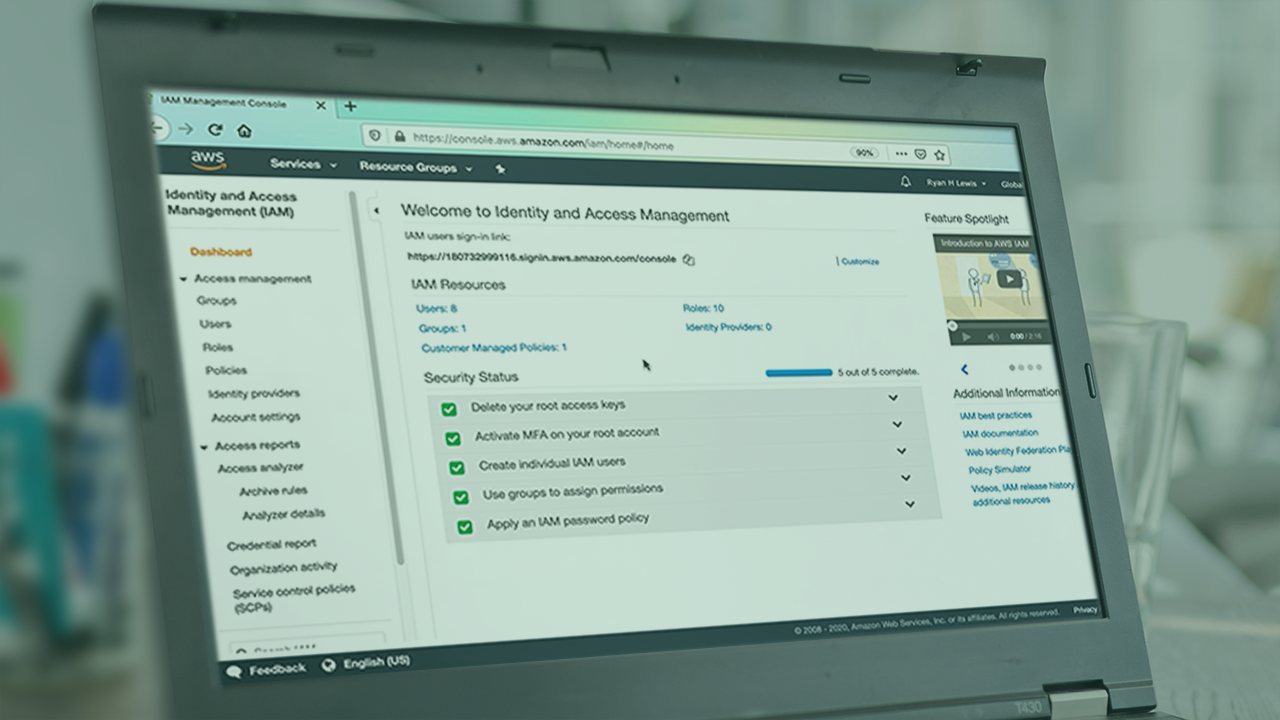
Amazon Web Services (AWS) gives you a lot of options for deploying applications and securing your resources. This course will give you experience using the best methods of deployment and how to use AWS security services to protect your account.
- Course
AWS Developer: Deployment and Security
Amazon Web Services (AWS) gives you a lot of options for deploying applications and securing your resources. This course will give you experience using the best methods of deployment and how to use AWS security services to protect your account.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Cloud
- Security
What you'll learn
AWS gives developers a lot of options, but it can be overwhelming to know the best way to deploy applications or how to secure your resources. In this course, AWS Developer: Deployment and Security, you will gain the ability to effectively deploy applications to AWS and secure your AWS infrastructure. First, you will learn how to efficiently deploy resources and applications. Then, you will explore how to secure your resources in a VPC. Finally, you will discover how to use Users, Groups, and Roles to give permissions to your resources. When you’re finished with this course, you will have the skills and knowledge of AWS deployment and security needed to ensure your AWS resources are secure and maintainable.
AWS Developer: Deployment and Security
-
Introduction and Course Structure | 2m 51s
-
Deployment Strategies for AWS | 2m 58s
-
What Does Security in AWS Mean? | 2m 39s
-
The AWS Shared Security Model | 4m 23s
-
Essential Security Concepts in AWS | 3m 22s
-
What You Need for This Course | 1m 44s
-
Taking Hamster Security Seriously | 1m 20s
-
Conclusion | 1m 44s

