- Course
Network Infrastructure Protection for CCNP Security (300-206) SENSS
This course is part 2 of 6 in the Cisco CCNP Security (300-206) SENSS exam learning path. This course teaches one to secure the network infrastructure running Cisco IOS and ASAs, while also covering objectives of the CCNP Security (300-206) SENSS exam.
- Course
Network Infrastructure Protection for CCNP Security (300-206) SENSS
This course is part 2 of 6 in the Cisco CCNP Security (300-206) SENSS exam learning path. This course teaches one to secure the network infrastructure running Cisco IOS and ASAs, while also covering objectives of the CCNP Security (300-206) SENSS exam.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
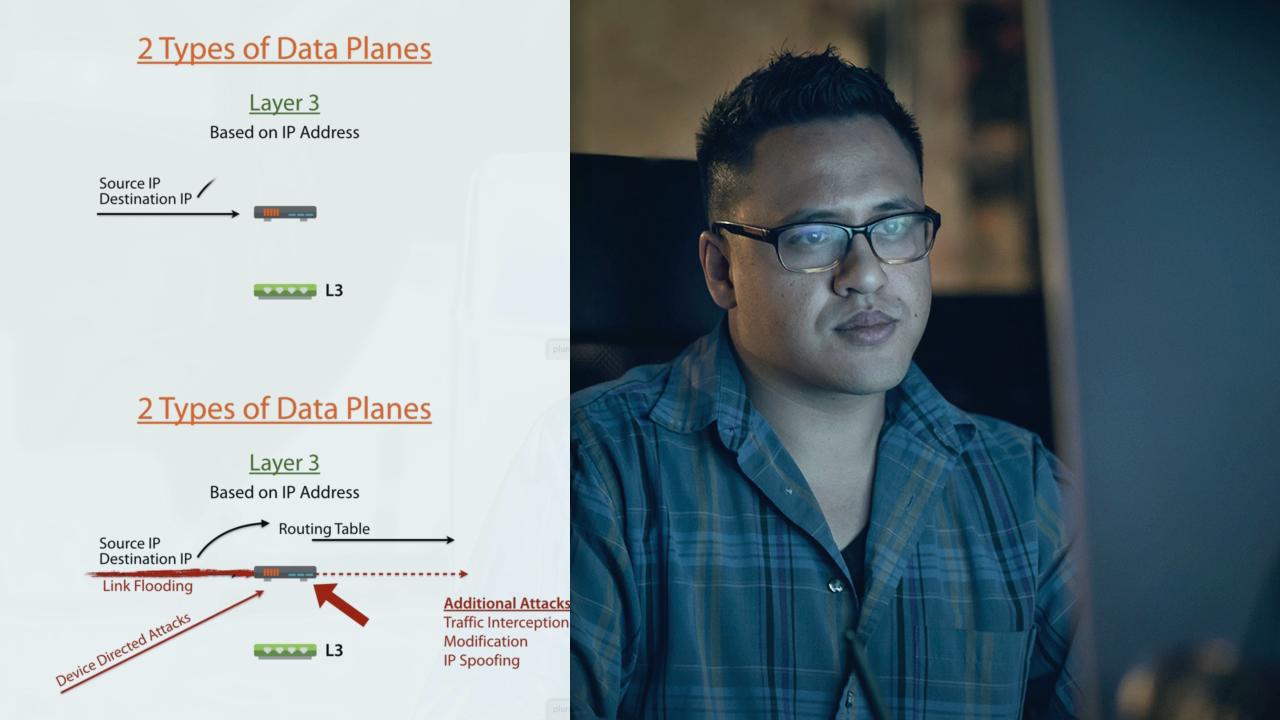
The network infrastructure is critical to enterprise businesses today. If compromised, business processes cease to function resulting in great expense, loss of reputation, and countless other effects over time. This course teaches one how to secure the network infrastructure on Cisco IOS router and Cisco Adaptive Security Appliances (ASA). This course also covers topics and objectives of the CCNP Security (300-206) SENSS exam.

