- Course
Collection with PowerUpSQL
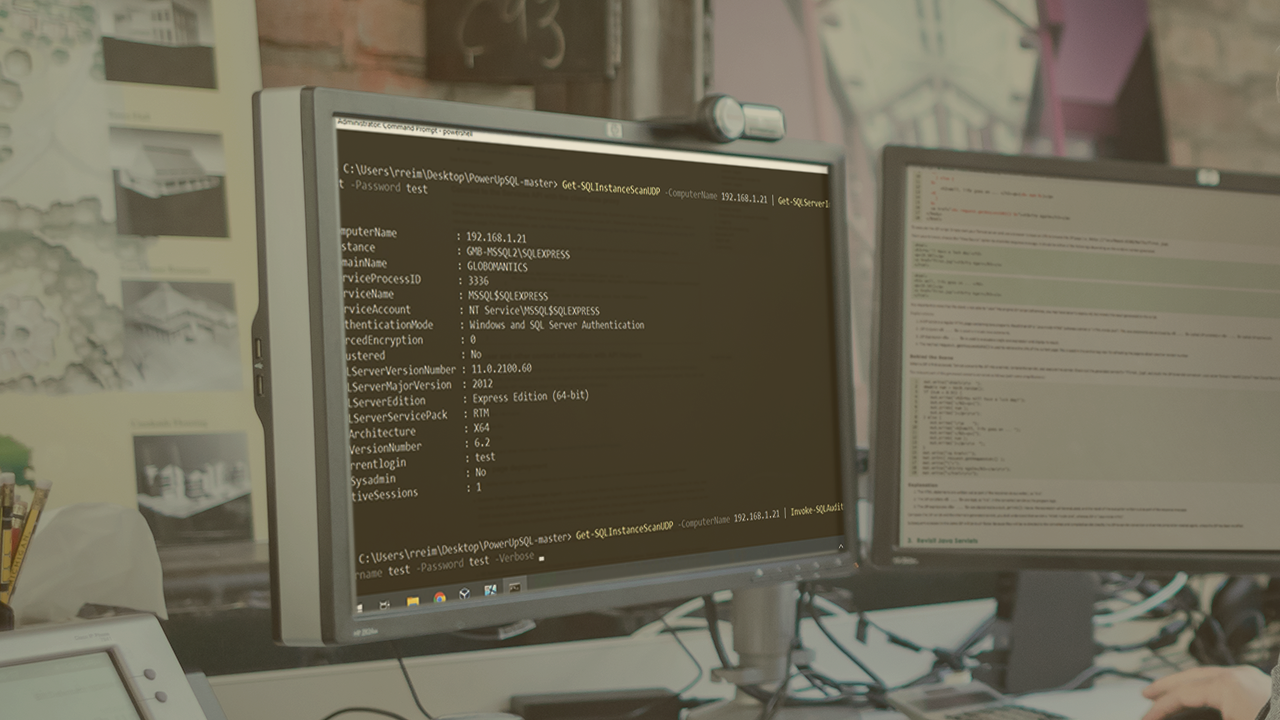
In a red team engagement, it is crucial to collect sensitive information to demonstrate the impact of a cyber attack to your client. This course will teach you how to collect sensitive data from Microsoft SQL databases using the PowerUpSQL tool.
- Course
Collection with PowerUpSQL
In a red team engagement, it is crucial to collect sensitive information to demonstrate the impact of a cyber attack to your client. This course will teach you how to collect sensitive data from Microsoft SQL databases using the PowerUpSQL tool.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
An important step on a red team engagement is collecting sensitive information. By demonstrating what kind of data a hacker could have access to, your client can better understand the impact of a real cyber-attack. In this course, Collection with PowerUpSQL, you will cover one of the most important tools for exploiting Microsoft SQL databases, the PowerUpSQL framework. First, you will learn how to get access to the database by discovering weak credentials in your target. Next, you will explore how to find and collect sensitive data in the database, including credit card information and stored passwords. Finally, you will see how to simulate a malicious attack of modifying stored data, hiding your tracks, and deleting entire tables. When you are finished with this course, you will have the skills and knowledge of PowerUpSQL needed to collect sensitive data from your target Microsoft SQL databases and cover four important tactics from the MITRE ATT&CK framework: Valid Accounts (T1078), Data from Local System (T1005), Stored Data Manipulation (T1492) and Data Destruction (T1485).

