- Course
Cyber Security Awareness: Digital Data Protection
This course will teach you some steps to better protect your data from cyber attacks.
- Course
Cyber Security Awareness: Digital Data Protection
This course will teach you some steps to better protect your data from cyber attacks.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
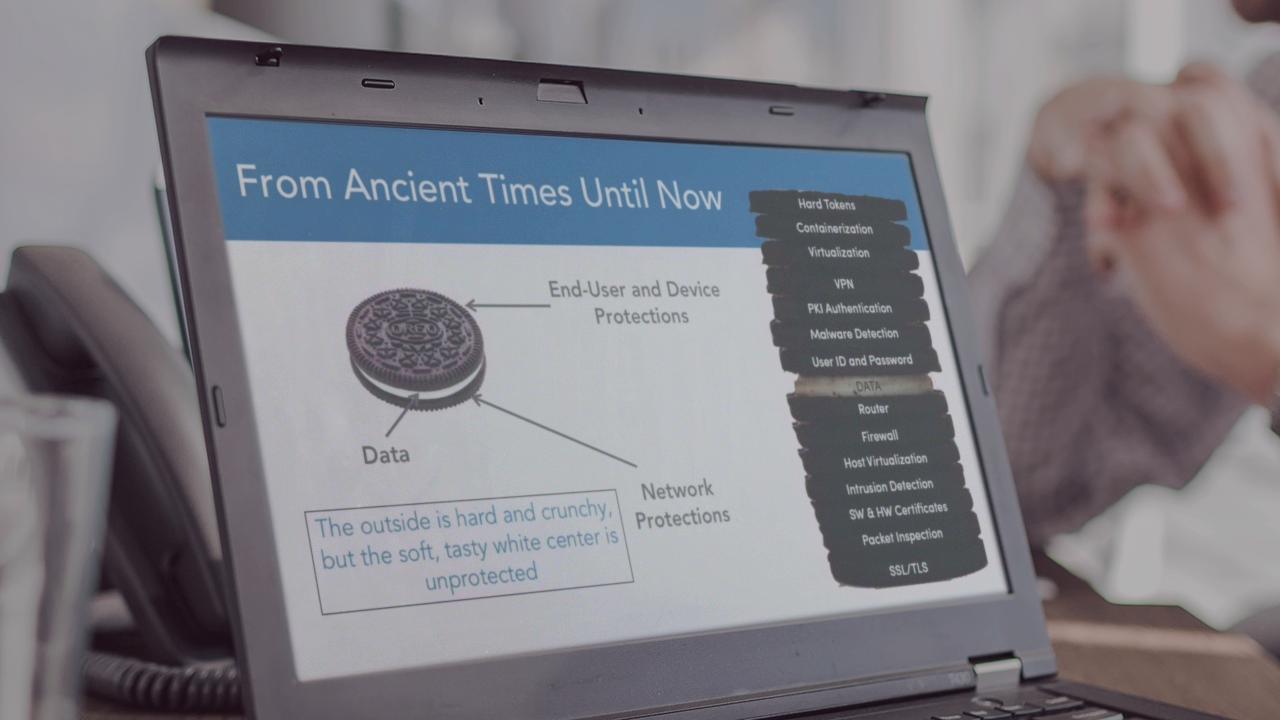
Malicious individuals getting access to your data is always something to be concerned about. This course, Cyber Security Awareness: Digital Data Protection, hopes to help alleviate some of those conerns. First, you will learn about the nature of data thefts today. Next, you'll dive into learning about digital data theft. Finally, you'll explore different fixes that are available to make your data usage safer. By the end of this course, you should feel more confident in your ability to protect you're own data.

