- Course
Getting Started with Zeek
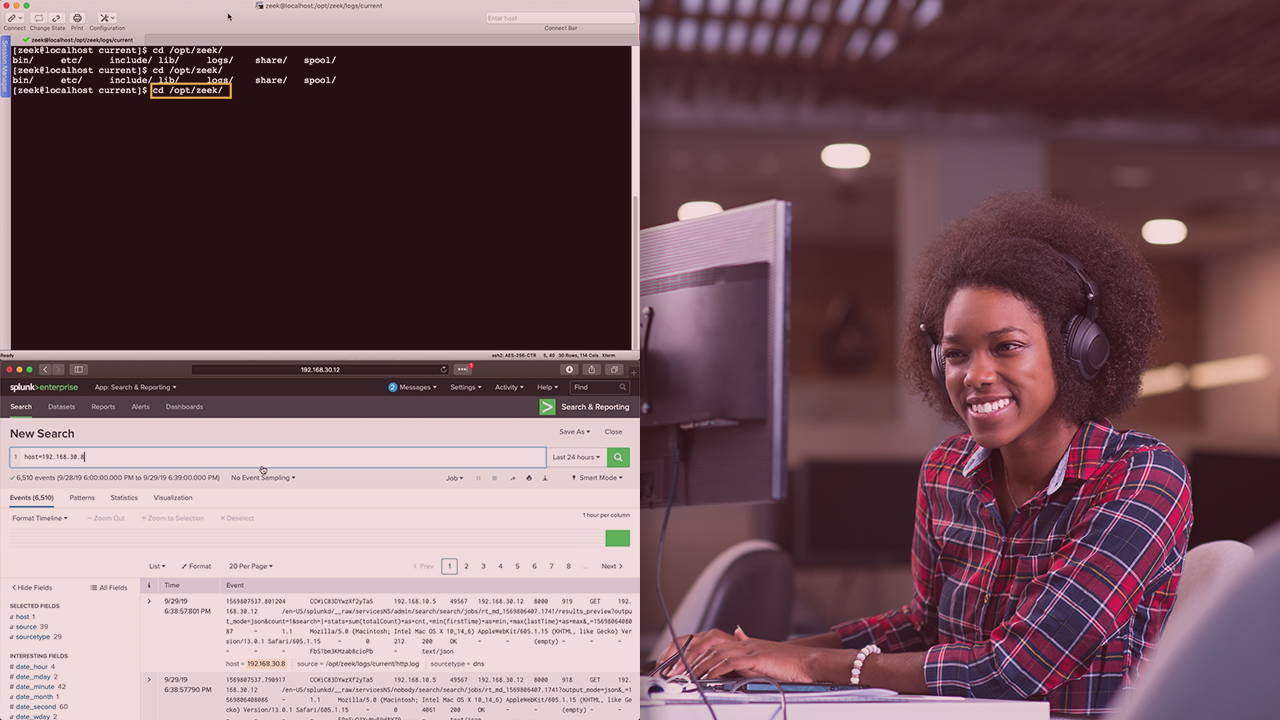
Zeek is a great open-source tool that allows you to monitor your network and analyze events within it. This course will teach you about this tool, and how to configure and use it within your network to suit your needs.
- Course
Getting Started with Zeek
Zeek is a great open-source tool that allows you to monitor your network and analyze events within it. This course will teach you about this tool, and how to configure and use it within your network to suit your needs.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Zeek is an event-based network monitoring and analysis tool used by many organizations. It enables users to see the traffic going through our networks and respond to it in different ways. Learning how to configure, use, and customize this tool will help you manage your network effectively. In this course, Getting Started with Zeek, you will learn all about this tool and how it functions, as well as how to use it. First, you will learn about the tool, it's purpose, and functionality. Next, you will learn about the pieces of the tool and how they interact with each other. Finally, you will explore the language Zeek uses and how you can use it to help your environment. When you're finished with this course, you will have a full understanding of the the tool and be able to use it effectively in your own network.

