- Course
Network Protocols for Security: ICMP
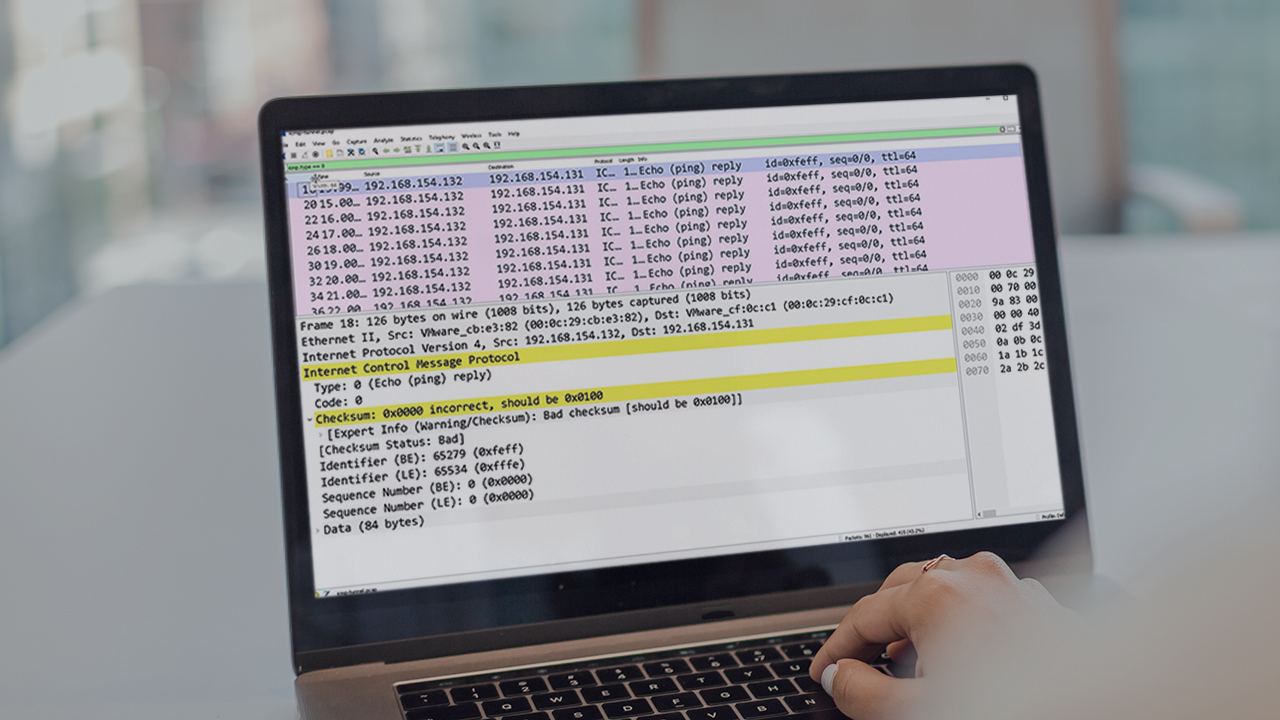
In this course, we’ll practice creating network traffic and inspecting the behavior of ICMP traffic. When you're finished, you'll have a fundamental understanding on how to find anomalies within ICMP.
- Course
Network Protocols for Security: ICMP
In this course, we’ll practice creating network traffic and inspecting the behavior of ICMP traffic. When you're finished, you'll have a fundamental understanding on how to find anomalies within ICMP.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Understanding how network protocols operate is an implied skill required to be successful in cyber security. In this course, Network Protocols for Security: ICMP, you’ll learn to analyze ICMP network traffic. First, you’ll explore sending some simple ICMP messages to analyze the protocol behavior. Next, you’ll discover how ICMP handles error messaging. Finally, you’ll learn how to detect malicious ICMP tunneling. When you’re finished with this course, you’ll have the skills and knowledge of ICMP needed to find anomalies and malicious activity amongst network traffic.

