- Course
Identity and Access Management on AWS: Users
This course explains the proper use of Users in AWS and why they should be used instead of the root account. It covers best practices, including MFA, and how federation can be implemented.
- Course
Identity and Access Management on AWS: Users
This course explains the proper use of Users in AWS and why they should be used instead of the root account. It covers best practices, including MFA, and how federation can be implemented.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Cloud
What you'll learn
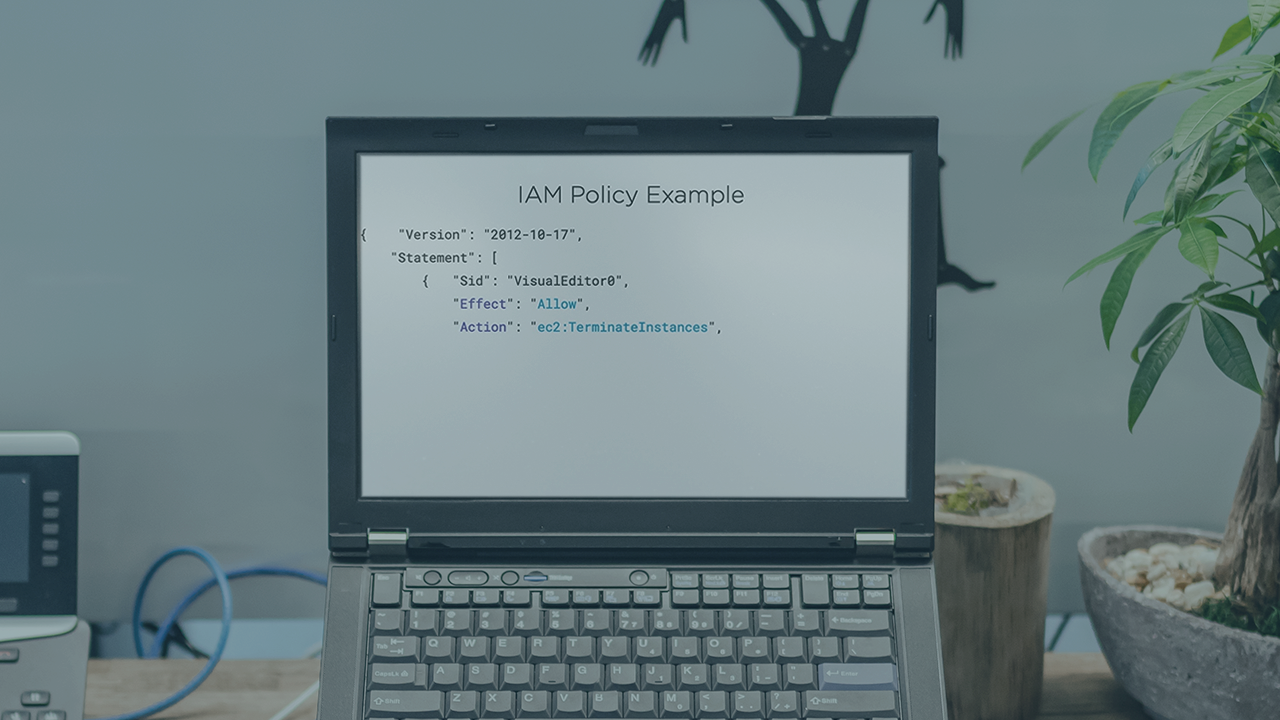
At the core of Identity and Access Management (IAM) usage in AWS is a thorough knowledge of users and their purpose. In this course, Identity and Access Management on AWS: Users, you’ll learn how to properly create and use IAM users and optionally federate them with external directory services. First, you’ll learn about the root user that is the only user in a new account and why this user should be used to set up the IAM user that will do the rest of the configuration. Next, you’ll explore how to create users for both Management Console and programmatic access, as well as how to secure that access. Finally, you’ll discover how to federate IAM in AWS with external authentication services, such as Active Directory and web identities (including Amazon, Google, and Facebook), as well as other frameworks like OpenID and SAML. When you’re finished with this course, you’ll have a foundational knowledge of users in IAM on AWS that will help you as you move forward with securing your AWS infrastructure.

