- Course
Implementing and Managing Office 365 Advanced Threat Protection
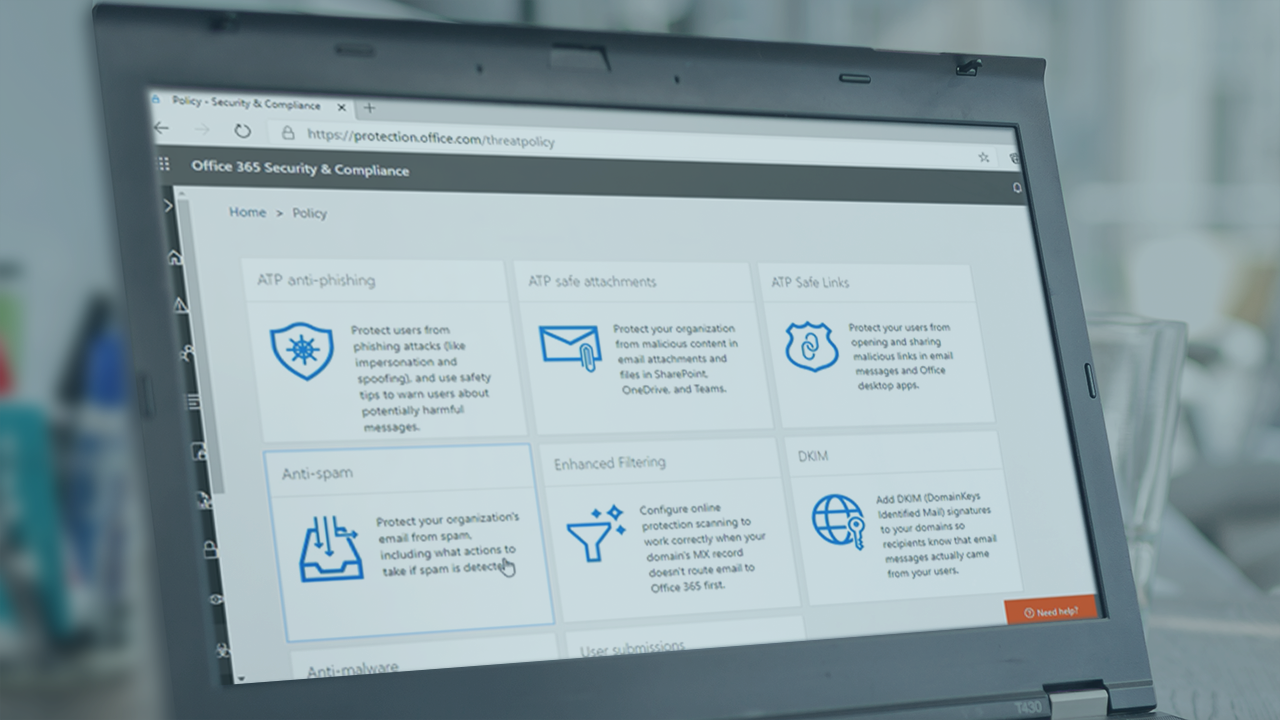
Environments are under constant attacks from constantly changing threats from spam, malware, and phishing attacks. This course will cover everything you need to get Office 365 ATP up and running in your environment.
- Course
Implementing and Managing Office 365 Advanced Threat Protection
Environments are under constant attacks from constantly changing threats from spam, malware, and phishing attacks. This course will cover everything you need to get Office 365 ATP up and running in your environment.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
Minute by minute, environments are under constant attacks from ever-changing threats. Spam, malware, and malicious links and URLs are bombarding users daily. To the rescue is Office 365 Advanced Threat Protection. In this course, Implementing Threat Protection with Office 365 Advance Threat Protection (ATP), you'll cover everything you need to get Office 365 ATP up and running in your environment. First, after a quick introduction to the capabilities, you’ll implement various threat protection tools in Office 365 ATP. Then, you'll explore tools for responding to and investigating breaches in your organization. When you're finished with this course, you'll have the skills and knowledge of Office 365 ATP needed to protect your organization.

