- Course
Information Gathering and Vulnerability Identification for CompTIA PenTest+
This course is a part 5 of the CompTIA PenTest+ series. You have identified the vulnerabilities, now you will use your toolset to identify how to exploit said vulnerabilities to prepare to for exploitation.
- Course
Information Gathering and Vulnerability Identification for CompTIA PenTest+
This course is a part 5 of the CompTIA PenTest+ series. You have identified the vulnerabilities, now you will use your toolset to identify how to exploit said vulnerabilities to prepare to for exploitation.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Cloud
What you'll learn
Now that you have finished identifying, enumerating, and uncovering vulnerabilities through your active and passive reconnaissance efforts, you have to now figure out what do with this data.
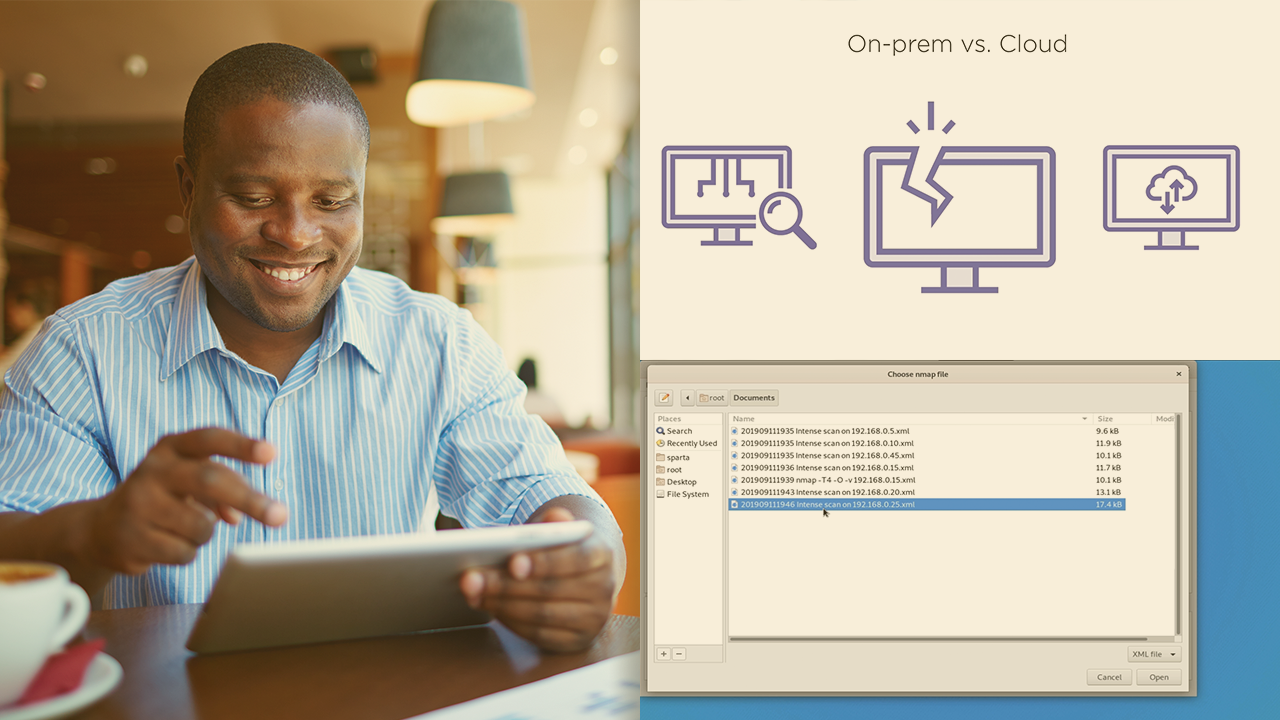
In this course, Information Gathering and Vulnerability Identification for CompTIA PenTest+, you will learn foundational knowledge of and gain the ability to analyze the vulnerabilities you've discovered. First, you will learn how to choose the right vulnerability scanner, be it open-source or commercial, on-prem or cloud-based. Next, you will discover how to organize said data by categorizing the assets, identifying false-positives and preparing for adjudication. Finally, you will explore how to transform this data into actionable exploits. When you’re finished with this course, you will have the skills and knowledge of analyzing the vulnerabilities or order to prepare for the next stage of the penetration testing lifecycle.

