- Course
Information Systems Auditing: Implementation
Far too many IT projects fail. The role of the auditor is to identify the symptoms of failure and allow management to address them in a timely manner. This course examines the processes of information systems implementation and operations.
- Course
Information Systems Auditing: Implementation
Far too many IT projects fail. The role of the auditor is to identify the symptoms of failure and allow management to address them in a timely manner. This course examines the processes of information systems implementation and operations.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
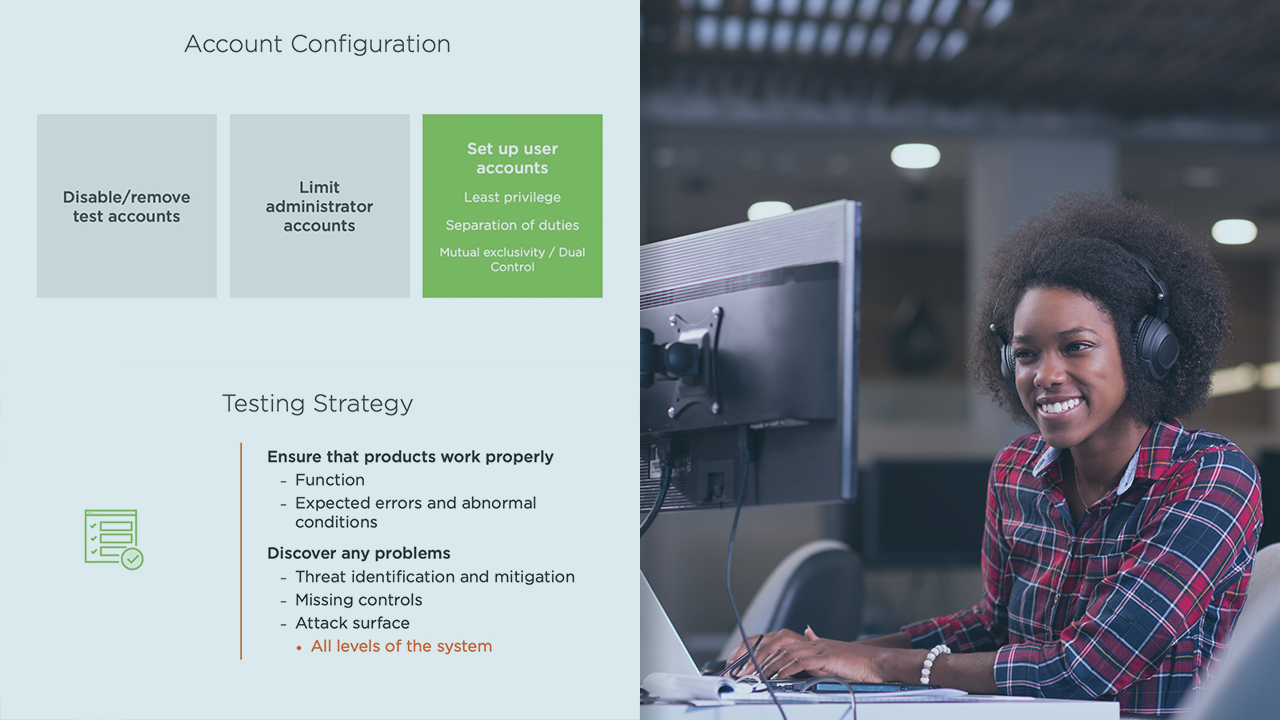
Many IT systems are designed to be secure but are not implemented correctly. This course, Information Systems Auditing: Implementation, will teach you the techniques of auditing the implementation of information systems. First, you will learn how to audit the process of testing and implementation. Then, you will discover how to ensure a secure deployment of the system. Finally, you will understand value of post-implementation review and feedback. By the end of this course, you will have a solid foundation of auditing the implementation of information systems.

