- Course
Learning the Essentials of CentOS Enterprise Linux 7 Administration
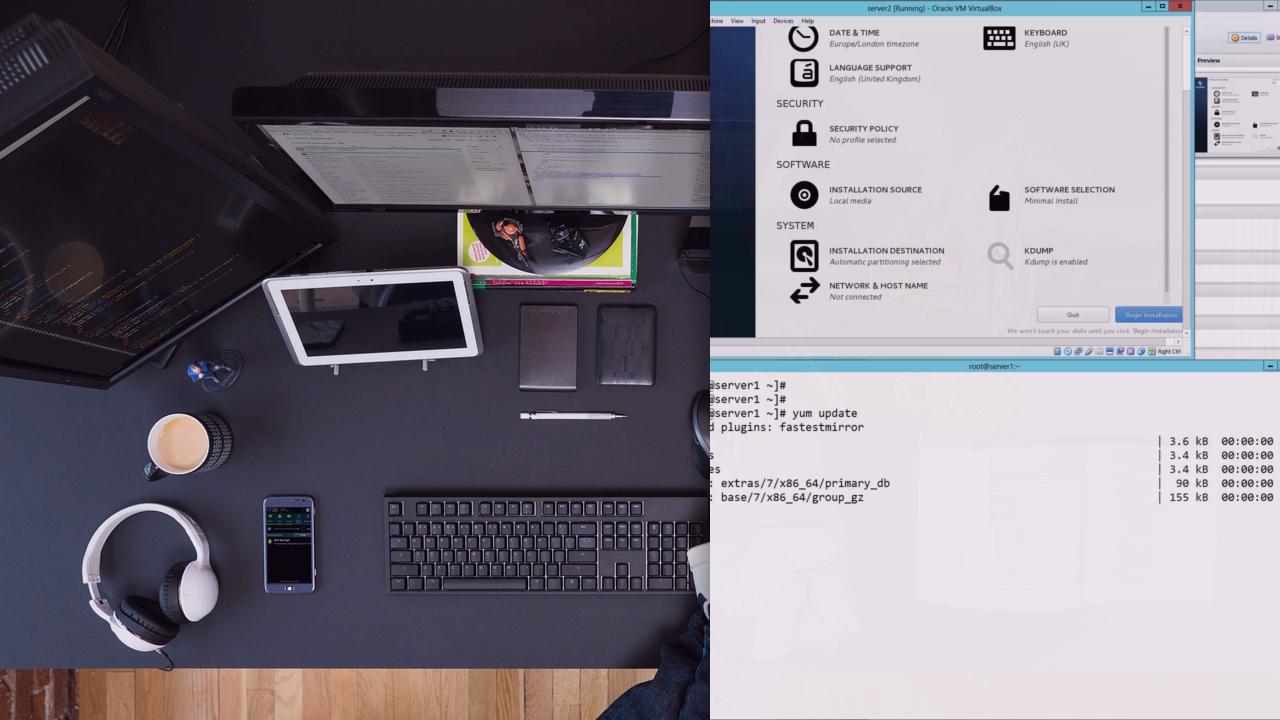
Preparing you for the practical exam based on the LFCS and RHCSA, you will learn Red Hat 7.
- Course
Learning the Essentials of CentOS Enterprise Linux 7 Administration
Preparing you for the practical exam based on the LFCS and RHCSA, you will learn Red Hat 7.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
This is the first in a series of courses designed to support the Linux Foundation Certified SysAdmin and the Red Hat Certified System Administrator practical exams. Based on CentOS 7.2, we get you started with installation before helping your though the basics of working on a CentOS 7 system.

