- Course
Linux Encryption Security
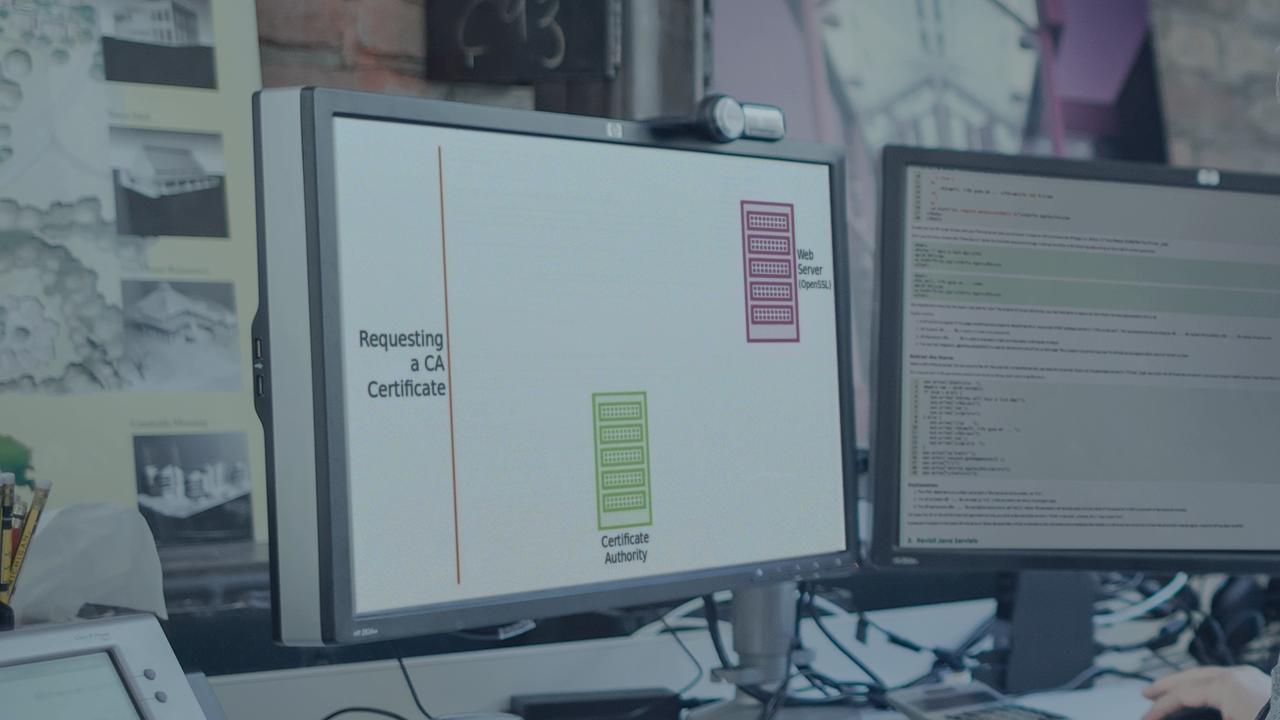
In this course, you'll learn how to properly secure your websites, data, and DNS infrastructure. You'll integrate industry-standard Linux encryption tools like OpenSSL with the X.509 public key certificate standard.
- Course
Linux Encryption Security
In this course, you'll learn how to properly secure your websites, data, and DNS infrastructure. You'll integrate industry-standard Linux encryption tools like OpenSSL with the X.509 public key certificate standard.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
If you're responsible for the security and reliability of IT resources of any kind, then encryption is your friend. Not only is it unwise to try to manage sensitive health records or credit card transactions without using strong encryption to obscure the data, but, in many cases, it's against the law. It's not only your data that's at risk; if your website and DNS service aren't protected by some kind of public key certificates, it could be just a matter of time before your servers will be hijacked by criminal hackers. In this course, Linux Encryption Security, you'll cover everything you need to know to apply proper encryption to the Linux systems behind your website, stored and mobile data, and DNS infrastructure. First, you'll learn how to configure and administrate industry-standard packages, such as OpenSSL, X.509 certificates, SSL/TLS, BIND, Apache httpd, eCryptfs, and Cryptsetup. Next, you'll explore encrypting the files on a PC or mobile device. Finally, you'll discover how to secure the all-important DNS service connecting your customers and users to your web-facing resources. By the end of this course, you'll feel confident tackling an assortment of possible security risk and vulnerabilities.

