- Course
Preparing to Manage Security and Privacy Risk with NIST's Risk Management Framework
Risk management is a critical element of security and compliance in today's IT infrastructures. This course will demonstrate the advanced skills you need to effectively manage cyber risk, security, and compliance with governance using the RMF.
- Course
Preparing to Manage Security and Privacy Risk with NIST's Risk Management Framework
Risk management is a critical element of security and compliance in today's IT infrastructures. This course will demonstrate the advanced skills you need to effectively manage cyber risk, security, and compliance with governance using the RMF.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
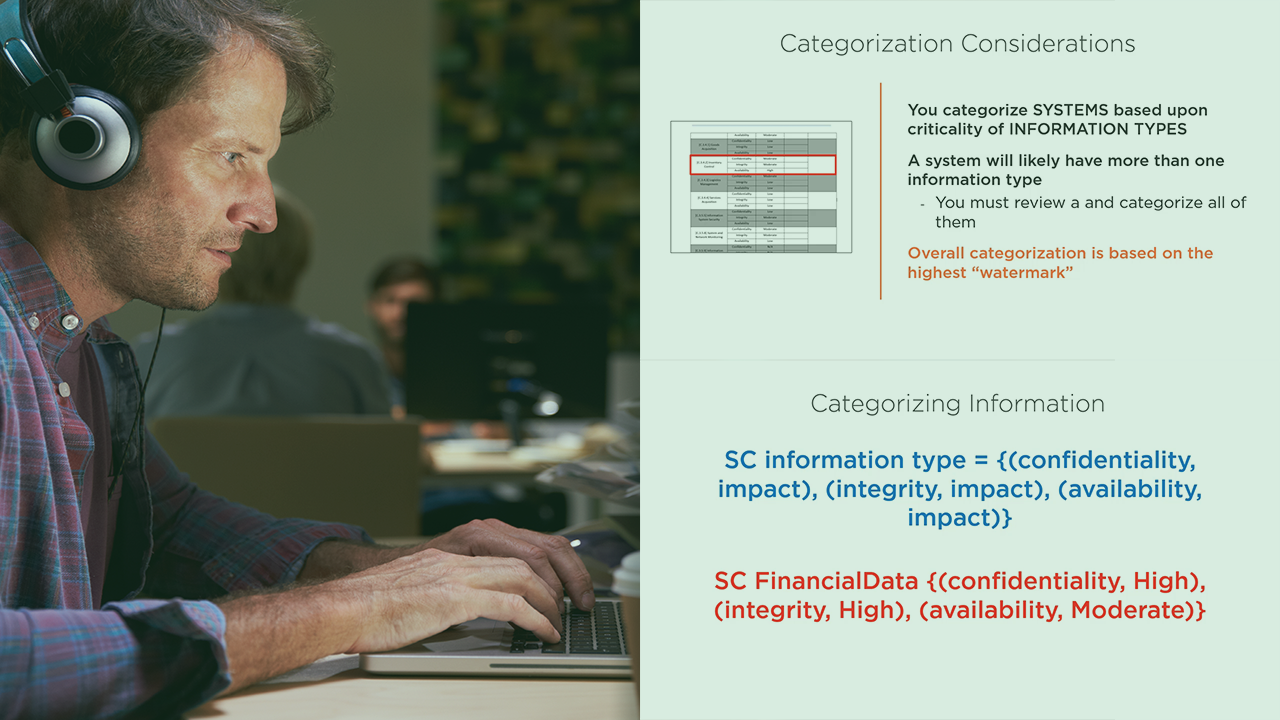
Risk is a necessary evil in today’s modern government, corporate, and private networks. Managing this risk is a careful balancing act between art and science, and focuses on three interrelated, critical aspects of systems: risk, system and data security, and compliance with governance. Organizations must have a proven methodology of managing cyber risk, security, and compliance. In this course, Preparing to Manage Security and Privacy Risk with NIST's Risk Management Framework, you will continue your studies on the RMF beyond the fundamentals of the processes and procedures that make up the framework. You will gain the advanced knowledge necessary to apply the methods and techniques presented in the RMF to manage cyber risk in the “real world”. First, you will learn how to categorize systems based on the information they process and their criticality to the organization. You'll also learn how to manage risk stakeholder needs, and ensure that both the organization and the target systems are prepared to undergo the RMF lifecycle. Next, you will see how controls are baselined and implemented on systems, and how to realistically assess those controls. Finally, you will discover system accreditation decisions and how to make sure your system gets its Authorization to Operate, as well as conduct continuous risk monitoring. By the end of this course, you'll be thoroughly knowledgeable on what it takes to actually manage a system throughout its RMF lifecycle.

