- Course
Design Authorization for Microsoft Azure
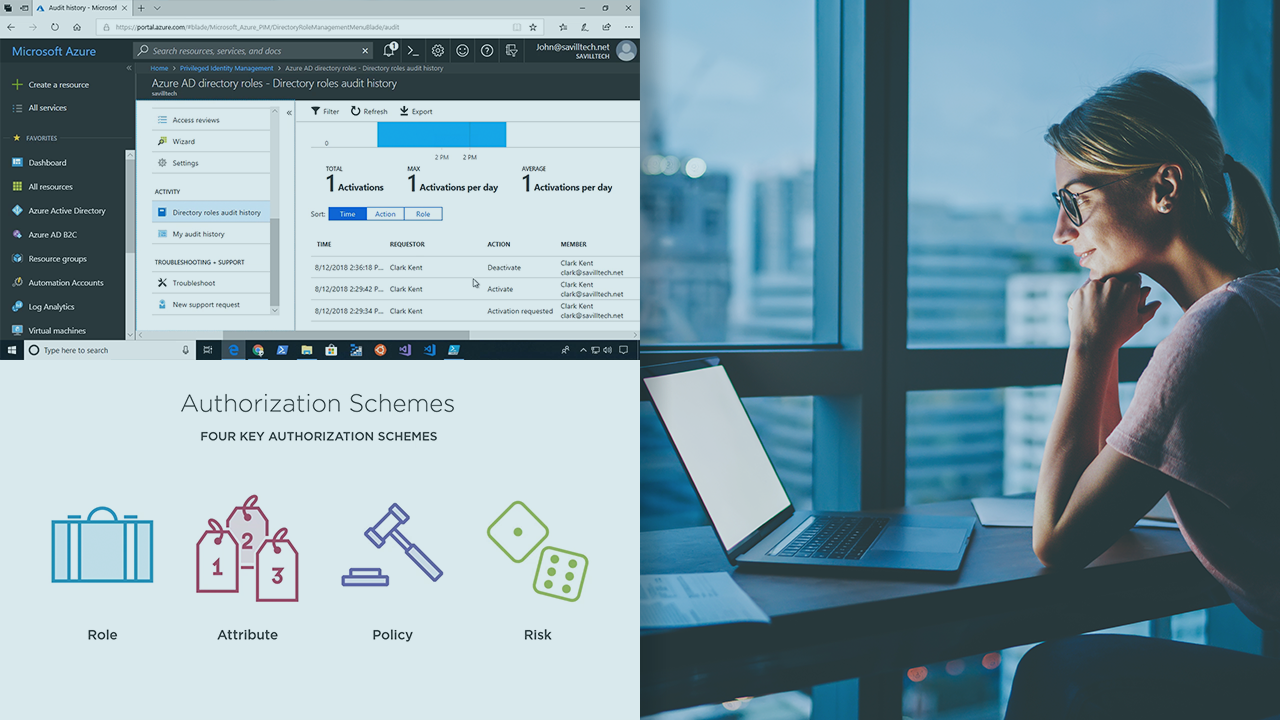
As Azure AD forms the foundation for identity in the cloud, authorization becomes the cornerstone of providing service access within Azure and across cloud services. This course teaches the authorization options available with Azure and Azure AD.
- Course
Design Authorization for Microsoft Azure
As Azure AD forms the foundation for identity in the cloud, authorization becomes the cornerstone of providing service access within Azure and across cloud services. This course teaches the authorization options available with Azure and Azure AD.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Cloud
What you'll learn
Authorization can be a very complex topic when looking at leveraging services across clouds via a centralized identity. In this course, Designing Authorization for Microsoft Azure, you will learn foundational knowledge of authorization with Azure and Azure AD. First, you will learn the key concepts around delegated authorization. Next, you will discover the authorization capabilities for Azure and Azure AD. Finally, you will explore how to integrate applications with Azure AD and control the delegation. When you’re finished with this course, you will have the skills and knowledge of authorization in Azure AD needed to enable you to securely and efficiently leverage Azure and other cloud services in a seamless manner.

