- Course
Microsoft 365 Security: Threat Protection Implementation and Management
This course will teach you how to plan, implement, and manage Microsoft’s Threat protection stack within your organization.
- Course
Microsoft 365 Security: Threat Protection Implementation and Management
This course will teach you how to plan, implement, and manage Microsoft’s Threat protection stack within your organization.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
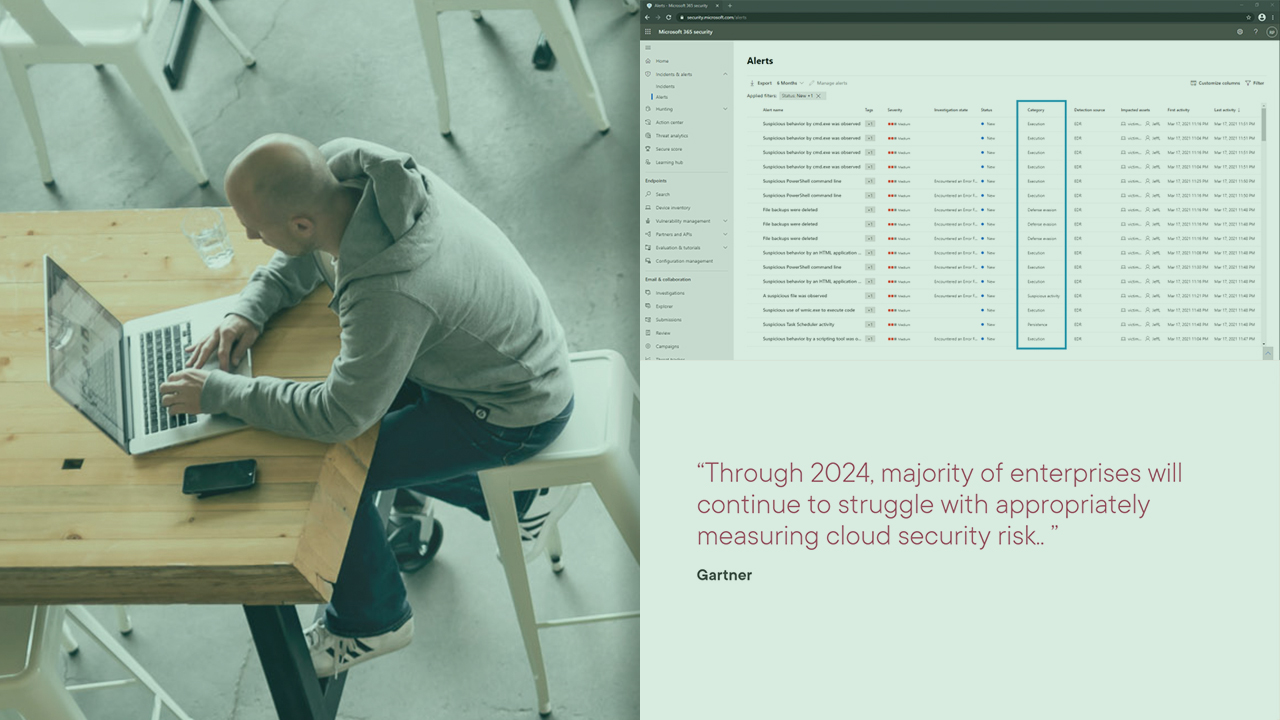
All organizations are targets for cyber attacks. As the threat landscape evolves, your security operations need to evolve too. In this course, Microsoft 365 Security: Threat Protection Implementation and Management, you’ll learn to implement and manage Microsoft’s Threat Protection stack. First, you’ll explore how to protect identities. Next, you’ll discover how to protect endpoints and Office 365. Finally, you’ll learn how to perform advanced hunting by pulling all the data together into a single pane of glass for incident management and advanced hunting. When you’re finished with this course, you’ll have the skills and knowledge of Microsoft’s Threat Protection stack needed to help you to protect against threats, ultimately reducing your attack surface.

