- Course
Network Fundamentals and Protocols
Pluralsight is not an official partner or accredited training center of EC-Council. IPv4 is still the prevalent Internet protocol, but IPv6 is gaining traction. This course lays the foundation for securing network hardware and software.
- Course
Network Fundamentals and Protocols
Pluralsight is not an official partner or accredited training center of EC-Council. IPv4 is still the prevalent Internet protocol, but IPv6 is gaining traction. This course lays the foundation for securing network hardware and software.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
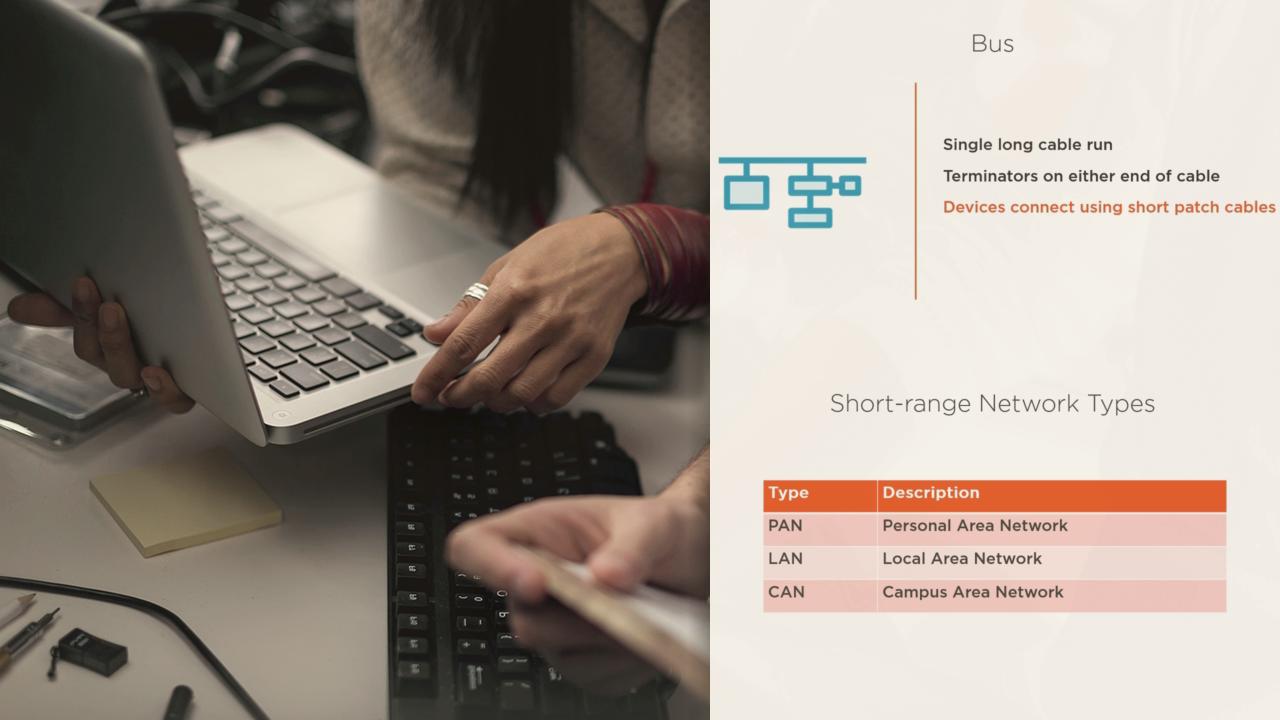
Pluralsight is not an official partner or accredited training center of EC-Council. Today's computing devices are always connected to a network. While increasing productivity, this also increases the risk of malicious activity. This course, Network Fundamentals and Protocols, begins by introducing you to network topologies and network equipment. Subsequently, you will learn about IPv4 and IPv6 addressing and protocols. Lastly, you will be introduced to the layers of computer network defense and secure network design. After finishing this course, you'll have an understanding of network hardware and software, and you'll be able to gain insights from captured network traffic.

