- Course
Network Security Basics
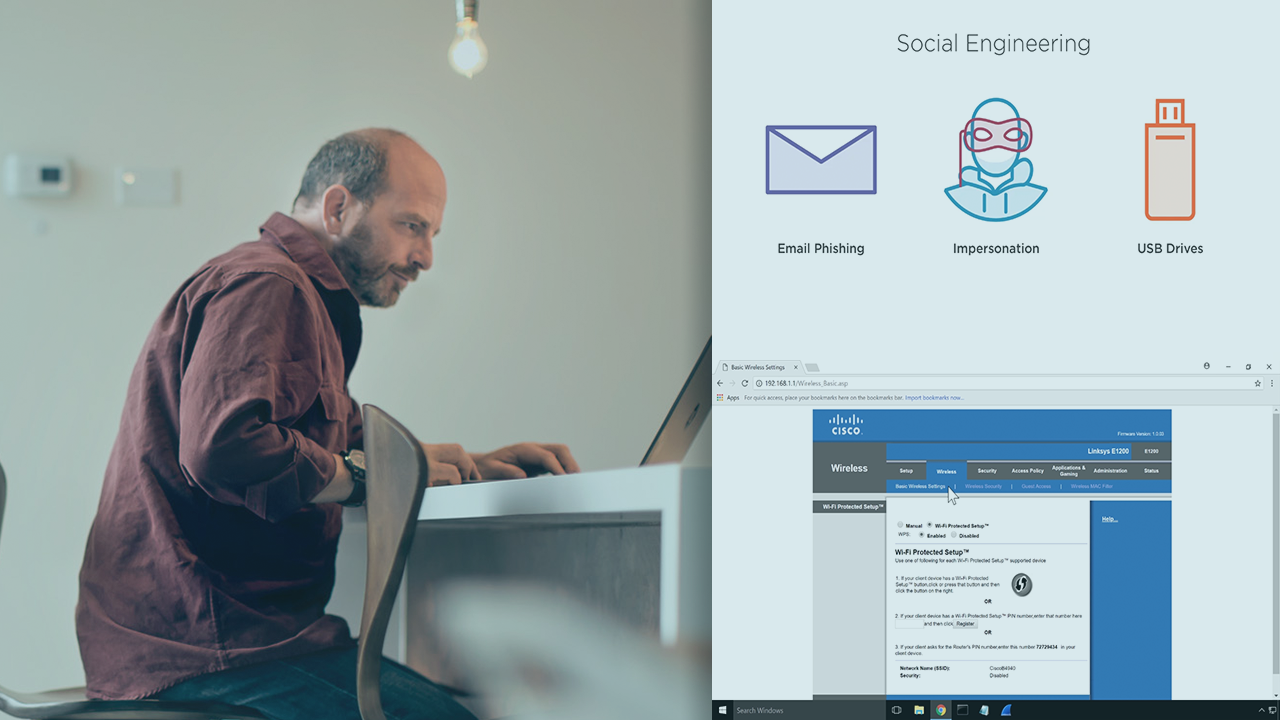
Data network security is more important than ever. This course will examine critical network attacks as well as tools, techniques, and policies that can help mitigate network attacks and data breaches.
- Course
Network Security Basics
Data network security is more important than ever. This course will examine critical network attacks as well as tools, techniques, and policies that can help mitigate network attacks and data breaches.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
Data breaches have become common place in national and world news, and because of this, engineers now find themselves in new roles in organizations, exclusively focused on securing information. In this course, Network Security Fundamentals, you will learn about the different types of attacks used to bring down networks, and/or steal data from them. First, you will examine the physical security of data centers, password creation recommendations, user account privileges, and devices to monitor network behavior. Next, you will learn about techniques for mitigating these attacks. Finally, you will learn about mechanisms for encrypting wireless traffic. By the end of this course, you will know the difference between WEP, WPA, WPA2, and how you can use multifactor authentication to prevent unauthorized account access.

