- Course
Getting Started with Packet Analysis
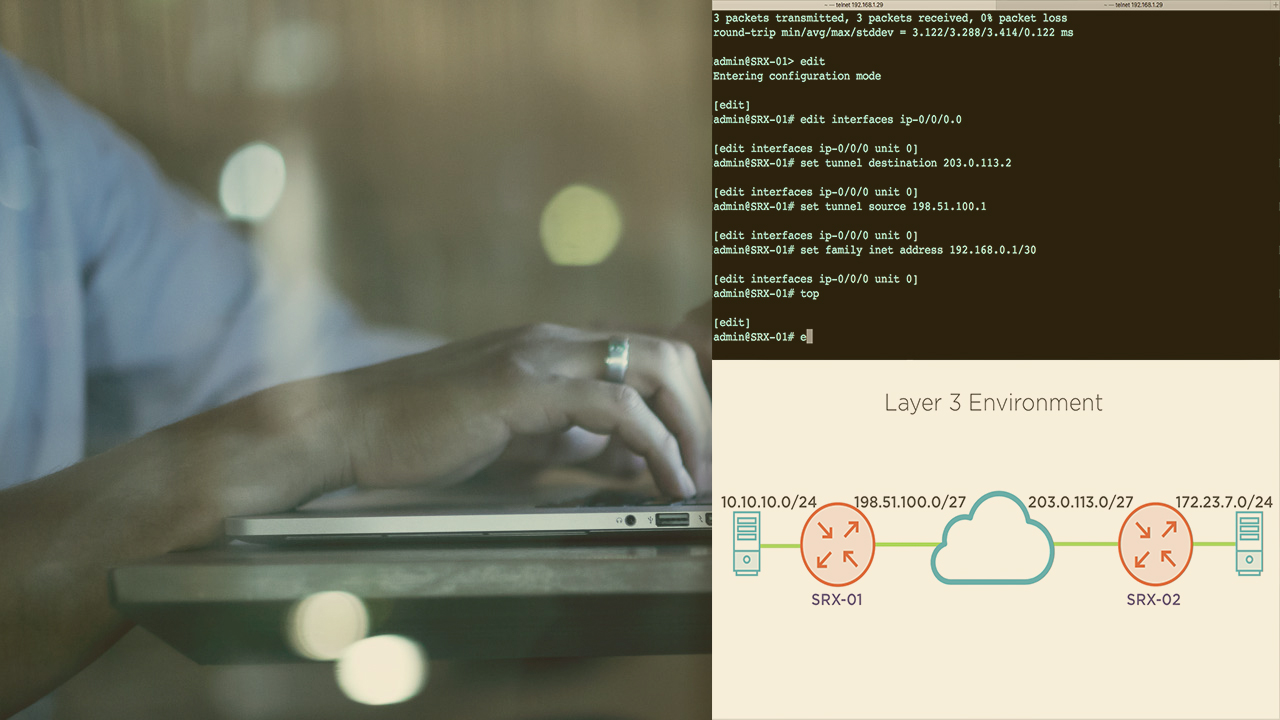
Do you know the kind of data that transmits across your network? This course will give you the knowledge and tools necessary to build the foundational knowledge needed to be able to capture, read, and interpret packets within your network.
- Course
Getting Started with Packet Analysis
Do you know the kind of data that transmits across your network? This course will give you the knowledge and tools necessary to build the foundational knowledge needed to be able to capture, read, and interpret packets within your network.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Threats are everywhere within your IT infrastructures. There are many security devices to help detect and prevent these threats, but what happens when you need to dig into the details? What happens when you’re faced with analyzing a threat, conducting a forensic investigation, or troubleshooting an issue? In this course, Getting Started with Packet Analysis, you will learn the basic skills needed to be able to capture, read, and interpret packets within your environments. First, you will learn the structure of datagrams in your environments. Next, you will explore how to use your analysis tools, and how to interpret the information within a datagram. Finally, you will discover how to identify certain risks by looking at datagrams. When you’re finished with this course, you will have the foundational knowledge to be able to hone your skills in interpreting data that crosses your network. Software required: Security Onion with netsniff-ng, tcpdump, and Wireshark.

