- Course
Performing Threat Modeling with the PASTA Methodology
Do you have a hard time mitigating threats to your applications? Are you confused how to employ threat modeling? This course will teach you how to effectively employ threat modeling to reduce the attack surface of your application. We will use case studies to effectively.
- Course
Performing Threat Modeling with the PASTA Methodology
Do you have a hard time mitigating threats to your applications? Are you confused how to employ threat modeling? This course will teach you how to effectively employ threat modeling to reduce the attack surface of your application. We will use case studies to effectively.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
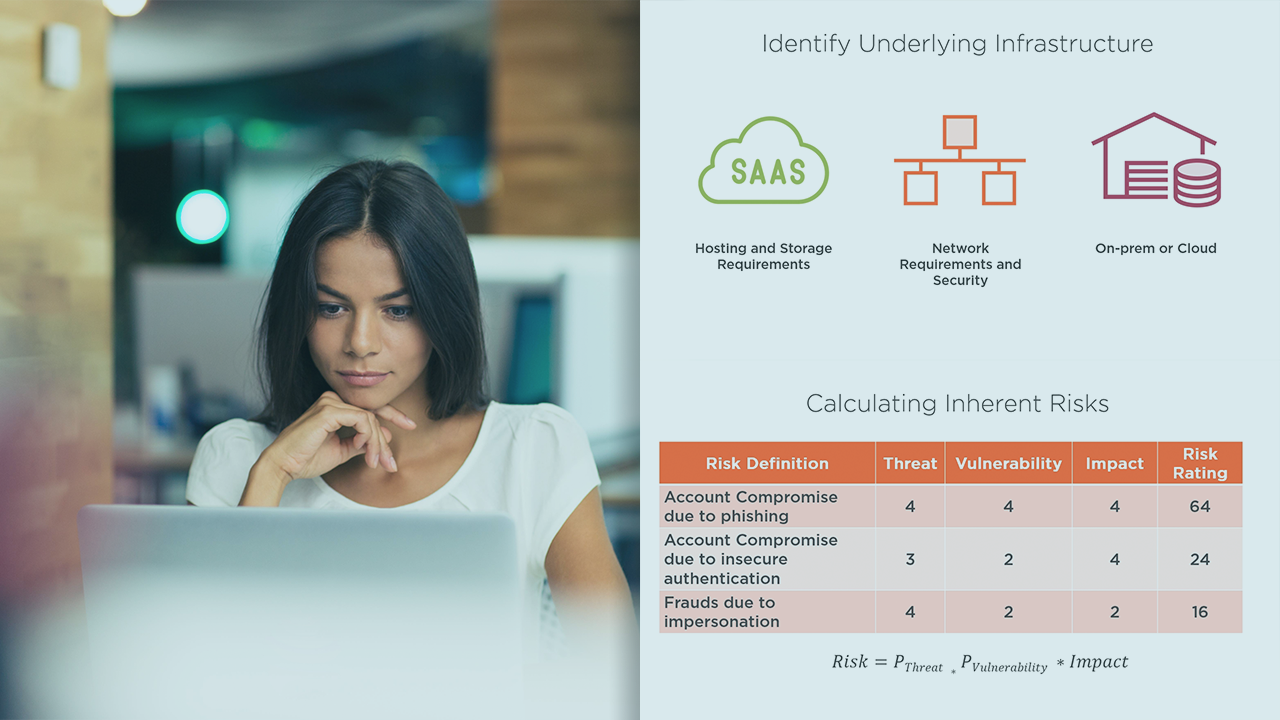
If you are familiar with threat modeling as an exercise, you would know that threat modeling involves identification of threats and vulnerabilities in the context of your applications. In this course, Performing Threat Modeling with the PASTA Methodology, you’ll learn to build application threat models using PASTA methodology. First, you’ll explore the fundamentals of threat modeling. Next, you’ll discover how to dissect applications into smaller components followed by threat, vulnerability, and weakness analysis. Finally, you’ll learn how to build attack models. When you’re finished with this course, you’ll have the skills and knowledge of PASTA methodology needed to conduct threat modeling.

