- Course
Risk Management and Information Systems Control: Risk Response and Mitigation
This course examines the various options available to respond to an identified risk. You will learn how to make the correct risk response decision to reduce risk to levels acceptable to management.
- Course
Risk Management and Information Systems Control: Risk Response and Mitigation
This course examines the various options available to respond to an identified risk. You will learn how to make the correct risk response decision to reduce risk to levels acceptable to management.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
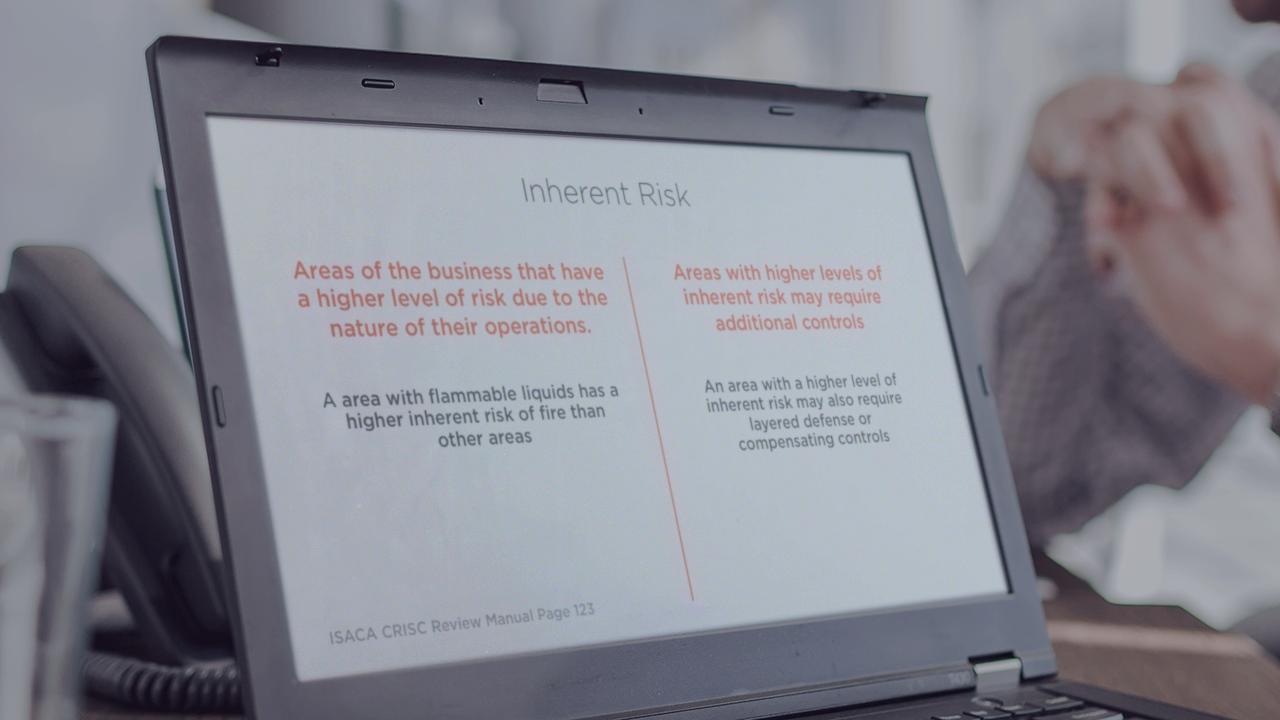
The development of a risk response strategy is based on many factors including cost, culture, other projects, and available resources. You will first examine the factors that influence the risk response decision and how to ensure that the risk faced by the organization is within management defined limits. Next, you will cover the topics of inherent risk, data protection, and data encryption. Last, you will look at risk areas to consider in your organization. By the end of this course, you will be one step closer to being prepared for the ISACA CRISC certification examination.

