- Course
Securing the Docker Platform
The Docker platform is a key ingredient in the packaging and delivery of container-based application services. This course will give you all the knowledge you need to enable you to securely manage the operation of a Docker platform.
- Course
Securing the Docker Platform
The Docker platform is a key ingredient in the packaging and delivery of container-based application services. This course will give you all the knowledge you need to enable you to securely manage the operation of a Docker platform.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
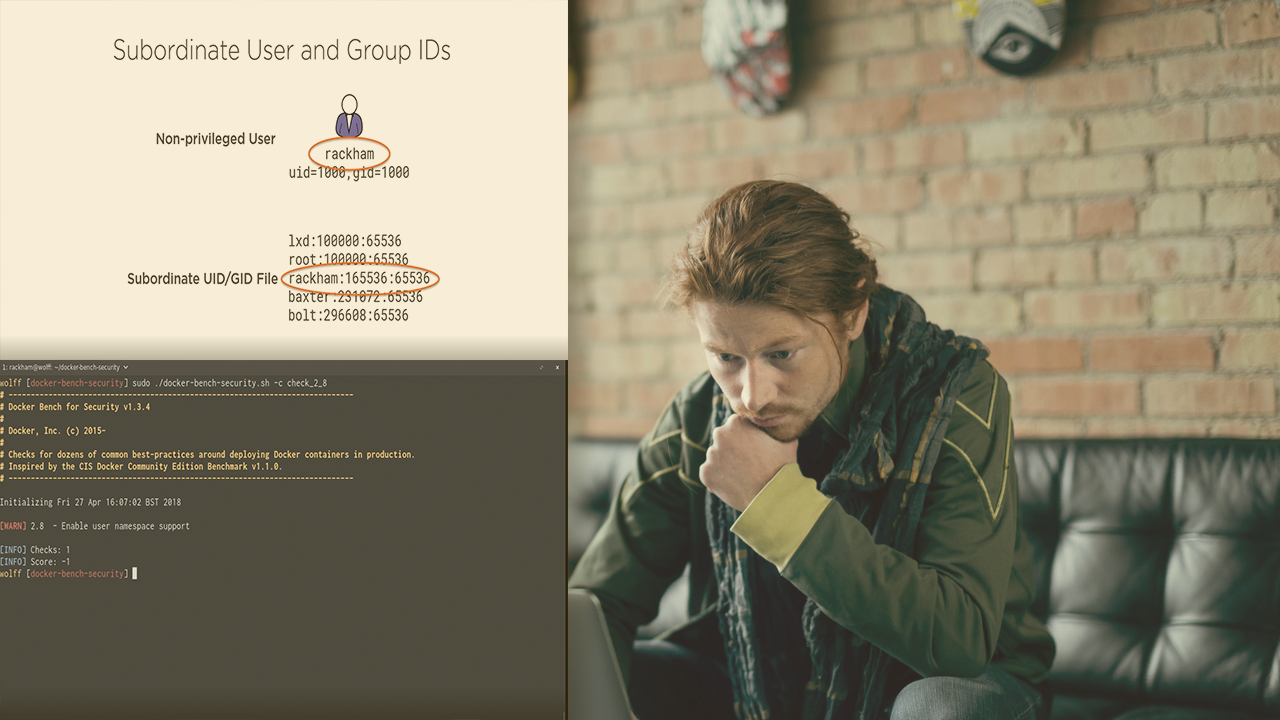
Docker containers are in widespread use as the distribution vehicle for cloud native application services. An important enabler in the process of building, packaging, and running those containers is the Docker platform, which is comprised of several parts. In this course, Securing the Docker Platform, you'll learn about the fundamental aspects of security that relate to the platform components. First, you'll gain a better understanding of the platform components involved and the means of measuring compliance against an industry benchmark standard. Next, you'll discover how to configure the Docker daemon for best practice security, as well as for more flexible access control and authentication. Finally, you'll explore how to apply security controls to other aspects of the platform including a self-hosted Docker registry and a Swarm cluster. By the end of this course, you'll have the necessary knowledge to configure, measure, and optimize effective Docker platform security.
Securing the Docker Platform
-
Version Check | 15s
-
Module Outline | 2m 47s
-
Defining the Docker Platform | 6m 34s
-
Acting on Docker Platform Security Vulnerabilities | 2m 5s
-
Determining What Needs to Be Secured | 7m 3s
-
Measuring How Secure a Docker Platform Is | 3m 8s
-
Testing a Docker Platform for CIS Docker Benchmark Compliance | 5m 24s
-
Module Summary | 1m 4s

