- Course
Securing Linux Servers
Linux is widely used to host critical services in Internet-facing settings. This course will show you how to take control of your servers, assess their vulnerability, and significantly reduce their attack surface by hardening the system.
- Course
Securing Linux Servers
Linux is widely used to host critical services in Internet-facing settings. This course will show you how to take control of your servers, assess their vulnerability, and significantly reduce their attack surface by hardening the system.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
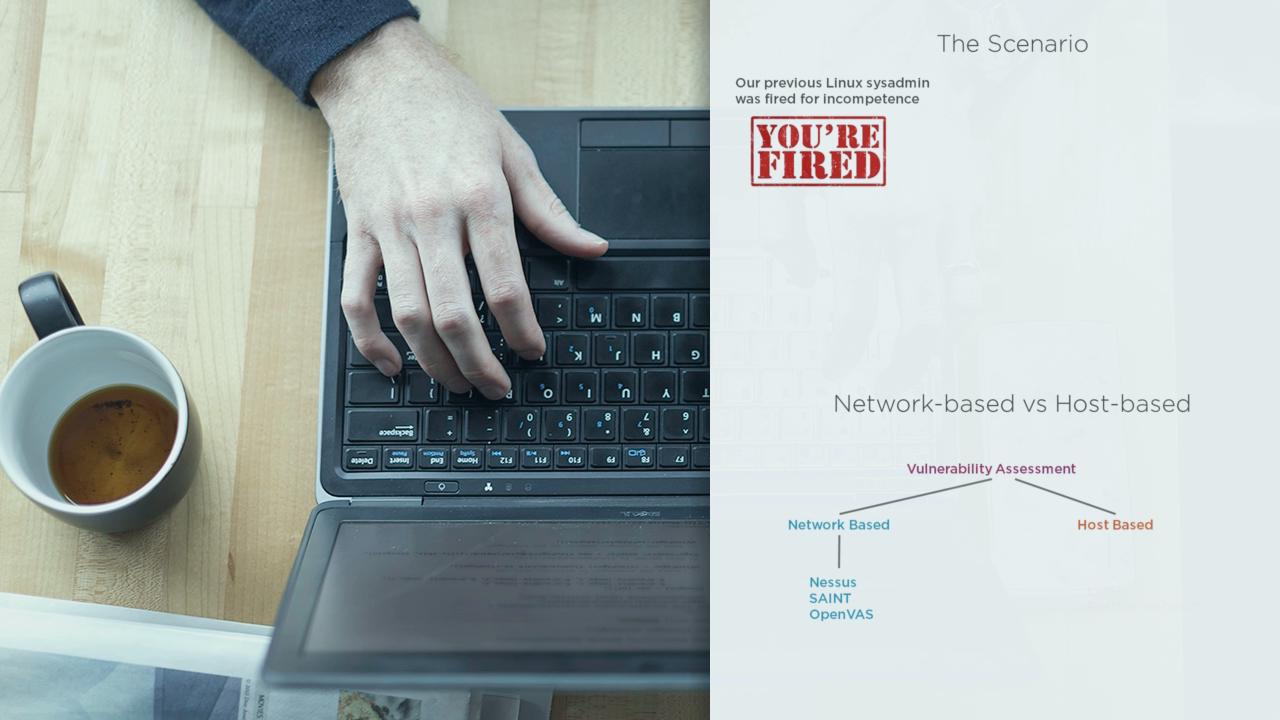
It is a fact of life that any server that connects directly to the Internet can be attacked. In this course, Securing Linux Servers, you'll learn best practices to reduce the attack surface of those systems. First, you'll learn to take control of booting your machines and see how to assess their vulnerability using a range of open-source tools. Next, you'll put into place some simple best practices to harden them and learn the benefits of SELinux in mitigating the potential damage of 0-day vulnerabilities. Finally, you'll learn how to check the integrity of your file system and detect suspicious activity. No training can claim to make your servers 100% secure, but after completing this course, you'll certainly be able to remove the low-hanging fruit from the reach of would-be attackers. The course uses CentOS7 or RHEL7, plus a number of readily-available open-source tools.

