- Course
Securing SSAS Models
This course explains the role-based security architecture of multidimensional and tabular models in SQL Server Analysis Services. You learn how to configure user or administrative access and granular security for conditional restrictive access.
- Course
Securing SSAS Models
This course explains the role-based security architecture of multidimensional and tabular models in SQL Server Analysis Services. You learn how to configure user or administrative access and granular security for conditional restrictive access.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Cloud
- Data
- Security
What you'll learn
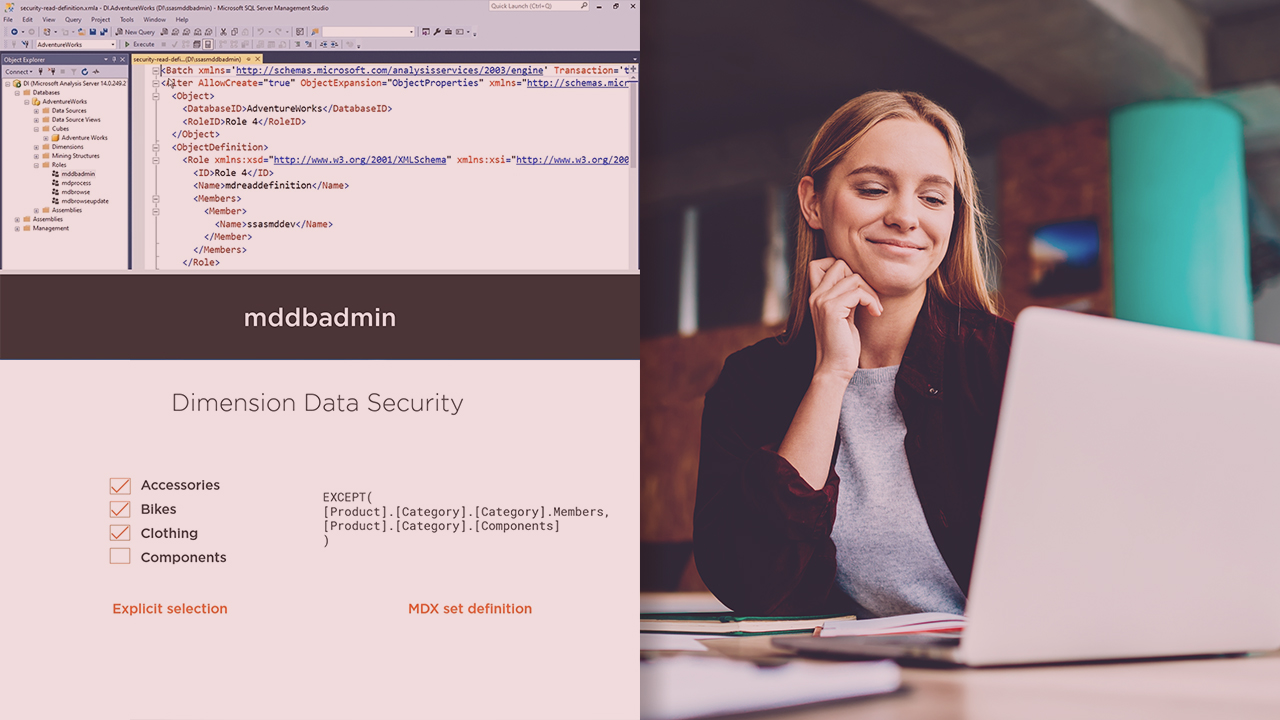
After you put a SQL Server Analysis Services multidimensional or tabular model into production, you need to manage what users can see and what users can do when interacting with the model. In this course, Securing SSAS Models, you will learn the options you have for implementing security. First, you will discover how default security works prior to explicitly configuring security, and then you will learn which tools you have at your disposal for managing security during development and following deployment to production. You will then explore the various security roles and test the effect of implementing each role type. Next, you will learn how to restrict roles from viewing sections of a model by using the security user interface. In addition, you will see firsthand what can happen when a user is assigned to multiple roles. Finally, you will walk through the process of implementing dynamic security to manage restrictions by using a table-driven approach. When you are finished with this course, you will have the needed skills and knowledge of Analysis Services security to properly set up security for your own models.

