- Course
Securing the Switch for Cisco CCNA 200-125/100-105
This course will describe some of the most severe switch security risks and discuss the mechanisms to help mitigate attacks through the well-known vectors.
- Course
Securing the Switch for Cisco CCNA 200-125/100-105
This course will describe some of the most severe switch security risks and discuss the mechanisms to help mitigate attacks through the well-known vectors.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
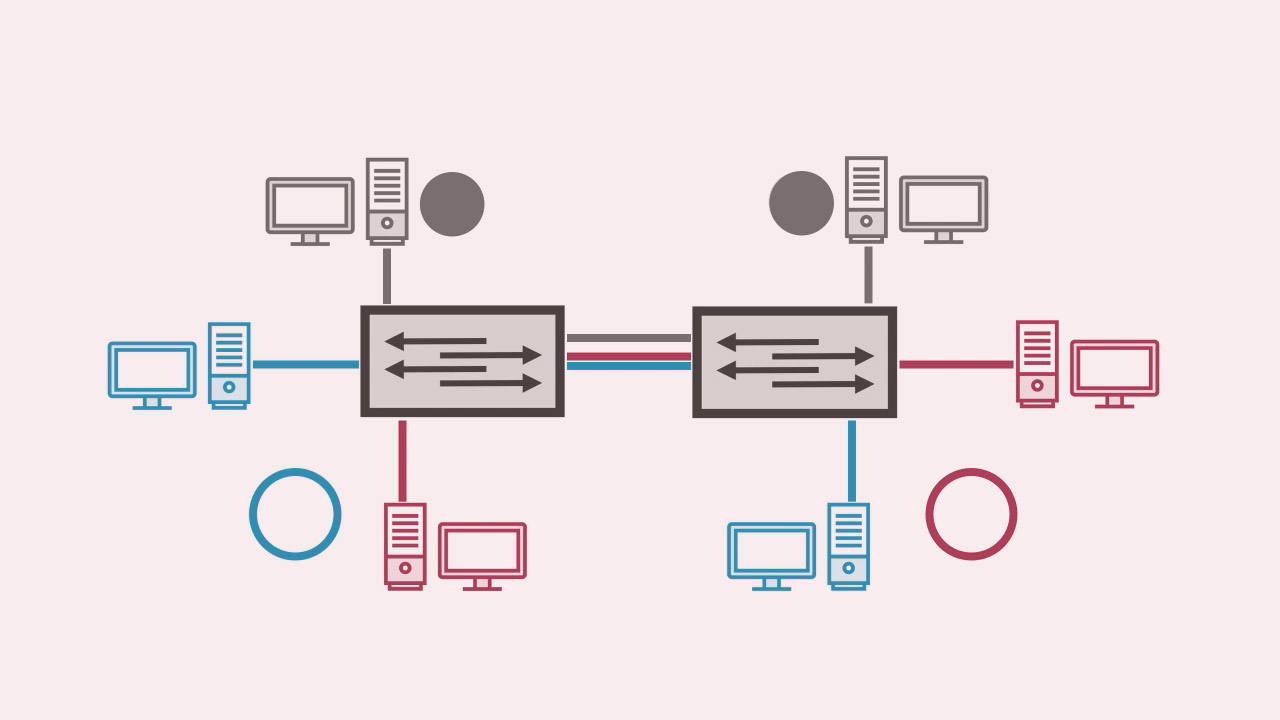
Switches are fantastic devices, allowing you to create VLANs, trunks, as well as offer fast and somewhat private communication. However, the basic nature of switch operation, as well as the advent of trunk links, VLAN tags and some backwards compatibility features, created some extra security risks that were not anticipated upon the advent of the technology. In this course, Securing the Switch for Cisco CCNA 200-125/100-10, you will start off by learning about frame double-tagging. Next, you'll move onto the native VLAN security issues and DTP. You'll wrap up the course with a demonstration of creating a secure base configuration for a switch. By the end of this course, you'll know how to put a secure base configuration on a switch, mitigating many layer 2 attacks against Ethernet.

