- Course
Security Operations: Provision, Baseline, and Monitor for CISSP®
This course will teach you the essential skills and knowledge required to manage an information security program. This includes the monitoring of controls and engineering an effective response to incidents.
- Course
Security Operations: Provision, Baseline, and Monitor for CISSP®
This course will teach you the essential skills and knowledge required to manage an information security program. This includes the monitoring of controls and engineering an effective response to incidents.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
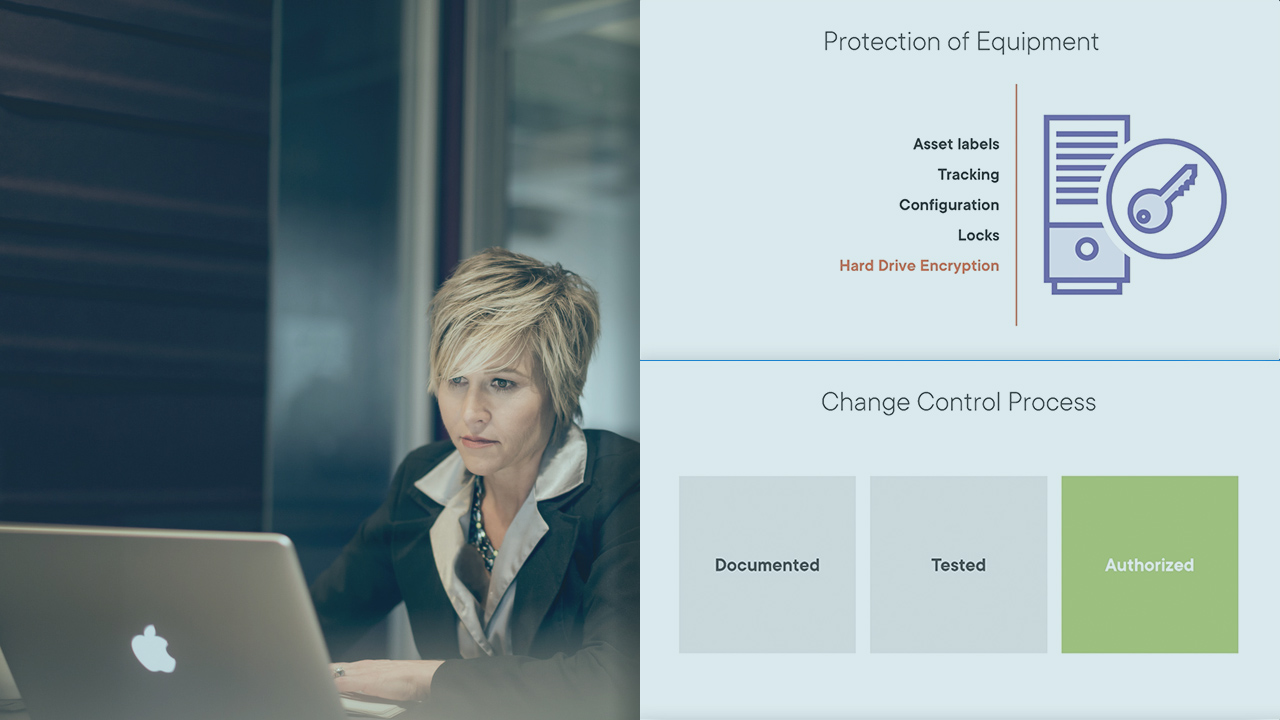
As an information security professional, skills in effective incident response and control monitoring will serve you well. In this course, Security Operations: Provision, Baseline and Monitor for CISSP®, you’ll learn to manage and lead an information security program. First, you’ll explore monitoring of security controls and networks. Next, you’ll discover change control and configuration management. Finally, you’ll learn how to monitor third-party relationships. When you’re finished with this course, you’ll have the skills and knowledge of security operations needed for the CISSP examination.

