- Course
Security Event Triage: Detecting Malicious Traffic with Signature and Session Analysis
Cyber attacks can take different forms and be performed by threat groups with different goals and methods. In this course, you will learn how signature and session analysis can be used to detect those attacks with network data.
- Course
Security Event Triage: Detecting Malicious Traffic with Signature and Session Analysis
Cyber attacks can take different forms and be performed by threat groups with different goals and methods. In this course, you will learn how signature and session analysis can be used to detect those attacks with network data.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
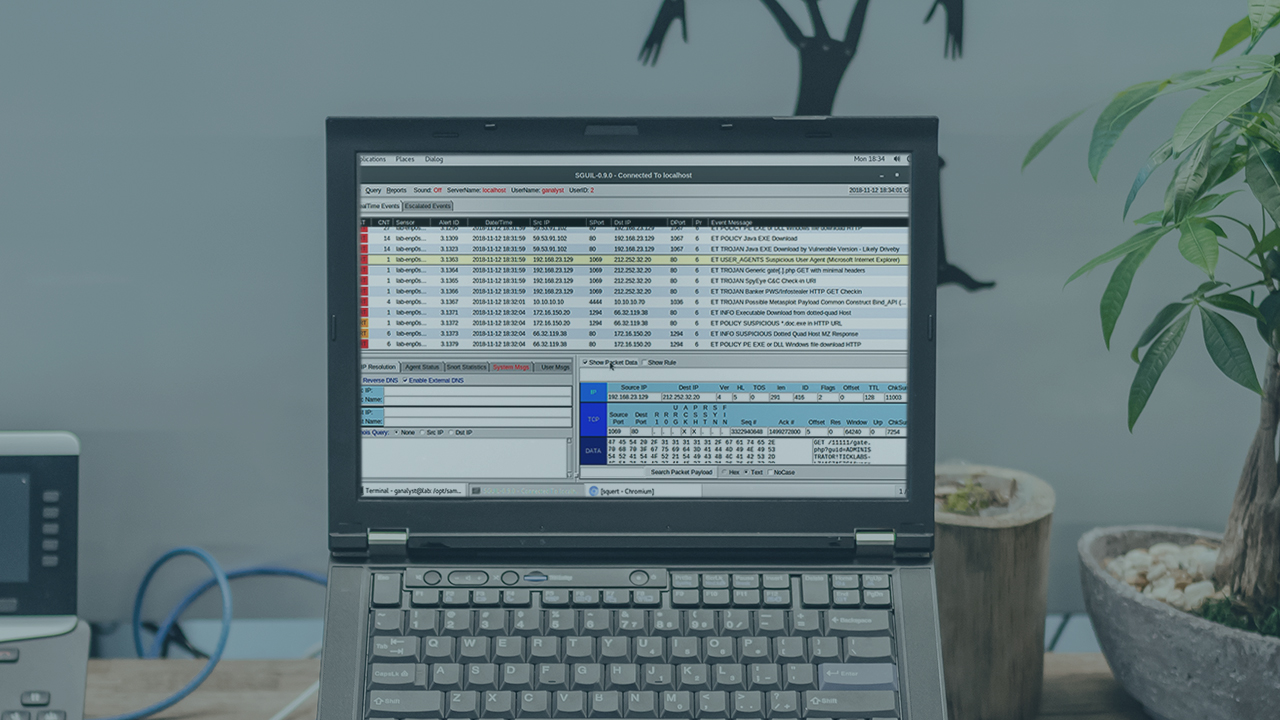
Cyber attacks evolve constantly, and detecting them requires the use of different techniques, some of which are more useful for specific scenarios than others. In this course, Security Event Triage: Detecting Malicious Traffic With Signature and Session Analysis, you will gain the ability to detect those attacks by leveraging signature and session analysis. First, you will learn how to detect attacks with common, detectable characteristics using signature analysis with tools like Snort. Next, you will discover how session analysis, with tools like Zeek and Kibana, can allow you to detect attacks by spotting suspicious behavior, in a way that is much harder to evade than simple signatures. Finally, you will explore how to detect suspicious patterns even in encrypted traffic, without the need to decrypt it. When you are finished with this course, you will have the skills and knowledge of signature and session analysis needed to detect attacks using network data.
This course is part of our Security Event Triage series which leverages MITRE ATT&CK to identify advance persistent threat tactics at all levels of the cyber kill chain.

