- Course
Security Event Triage: Detecting Network Anomalies with Behavioral Analysis
In this course on network behavioral analysis, you will explore the use of frequency, protocol, and population analysis methodologies to uncover events associated with multiple threat actors intrusions into a simulated enterprise network.
- Course
Security Event Triage: Detecting Network Anomalies with Behavioral Analysis
In this course on network behavioral analysis, you will explore the use of frequency, protocol, and population analysis methodologies to uncover events associated with multiple threat actors intrusions into a simulated enterprise network.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
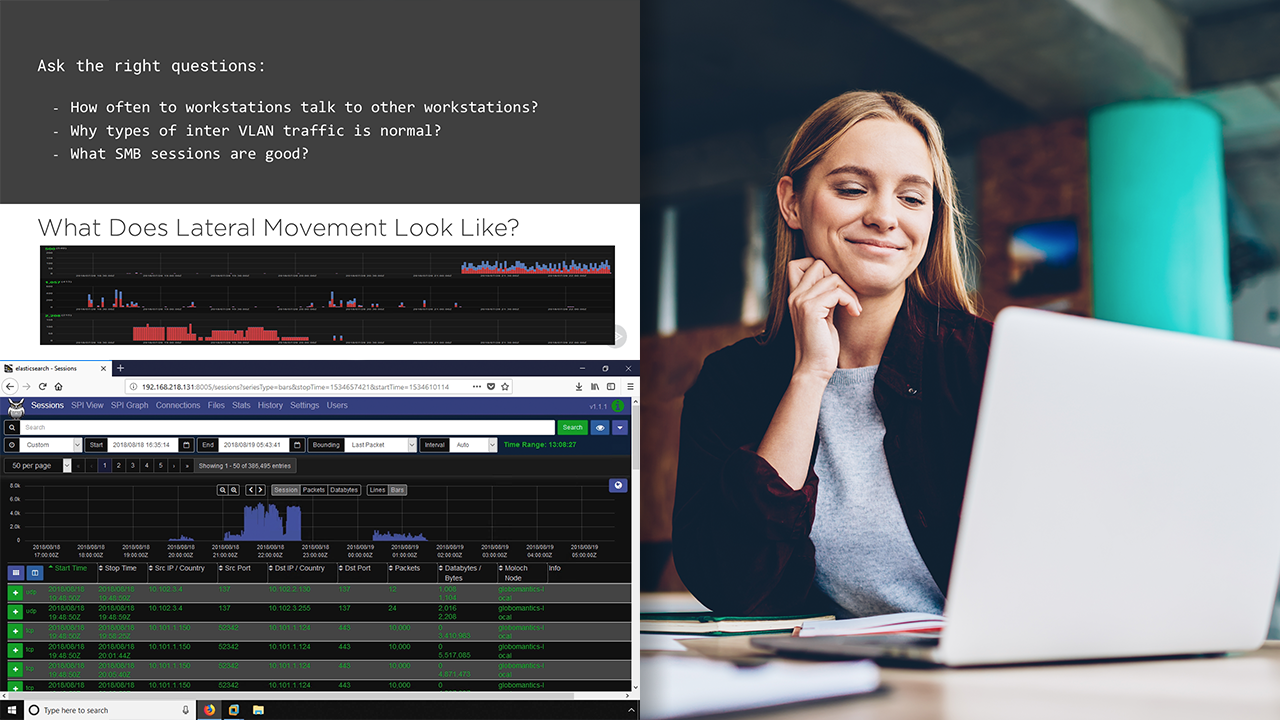
Developing the skills necessary for a security analyst to properly detect and triage advanced network intrusion tactics and techniques requires experience and the use of advanced detection capabilities. Neither of which are easily obtained. In this course, Security Event Triage: Detecting Network Anomalies with Behavioral Analysis, you will learn foundational knowledge required to separate good network traffic from bad and identify a myriad threat actor activity on an enterprise network. First, you will learn how to use frequency analysis to detect command and control, automated logins, and beaconing. Next, you will learn to leverage protocol analysis to identify DNS tunneling, anomalous HTTPS traffic, authentication brute forcing, and DHCP abuse. Finally, you will explore the use of population analysis by harnessing machine learning to identify HTTPS exfiltration and connect the dots associated with enterprise network intrusions. When you are finished with this course, you will have the skills and knowledge of network behavioral analysis needed to detect and triage events found at multiple levels of the cyber kill chain. Create your own network behavioral analysis workstation to follow along using your own environments data using the guide located here: https://github.com/arosenmund/pluralsight/tree/master/NBAD.
This course is part of our Security Event Triage series which leverages MITRE ATT&CK to identify advance persistent threat tactics at all levels of the cyber kill chain.

