- Course
SSCP®: Network and Communications Security
Learn to secure networks and telecommunications technologies.
- Course
SSCP®: Network and Communications Security
Learn to secure networks and telecommunications technologies.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
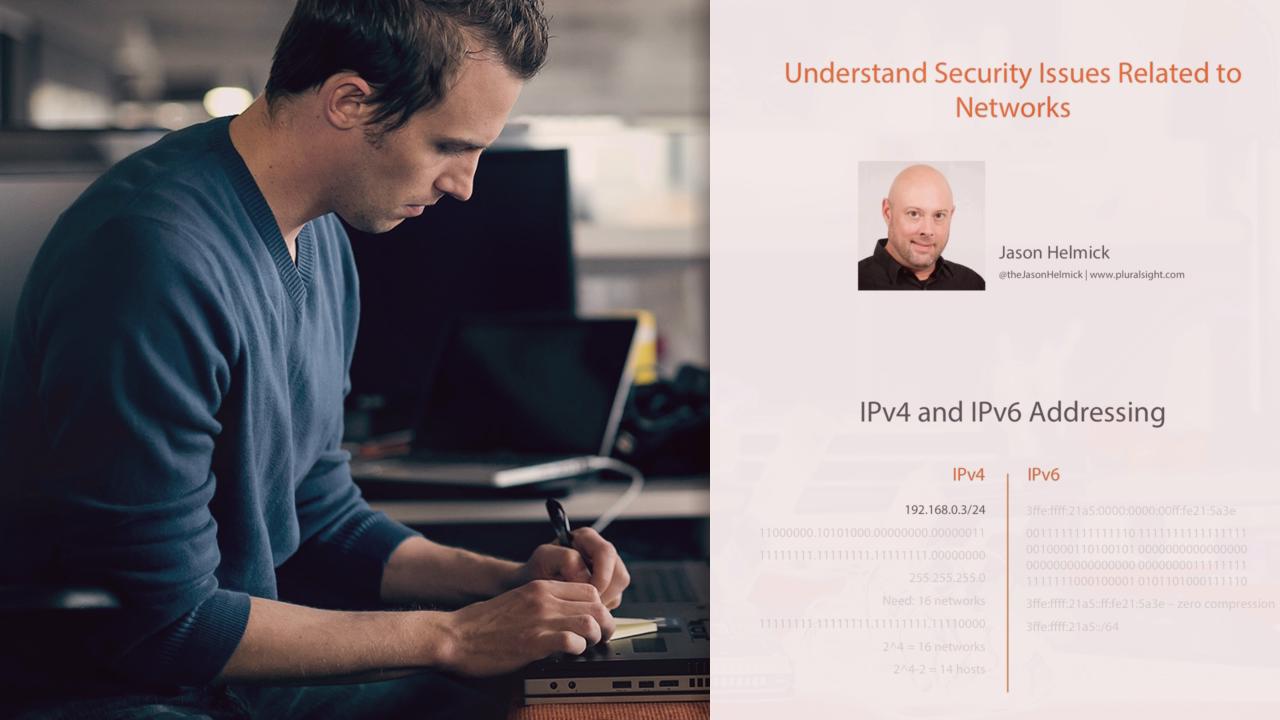
In this course, you will learn and explore Network and Communication Security. You will learn to understand security issues related to networks, protect telecommunications technologies, control network access, manage LAN-based security, operate and configure network-based security devices, and implement and operate wireless technologies.

