- Course
Testing Applications for CompTIA PenTest+
Part of any PenTest engagement application is an extremely high target. The reason is because of so many moving parts from operating systems all the way to even interfaces that are involved. In this course you will learn to check these components through testing.
- Course
Testing Applications for CompTIA PenTest+
Part of any PenTest engagement application is an extremely high target. The reason is because of so many moving parts from operating systems all the way to even interfaces that are involved. In this course you will learn to check these components through testing.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
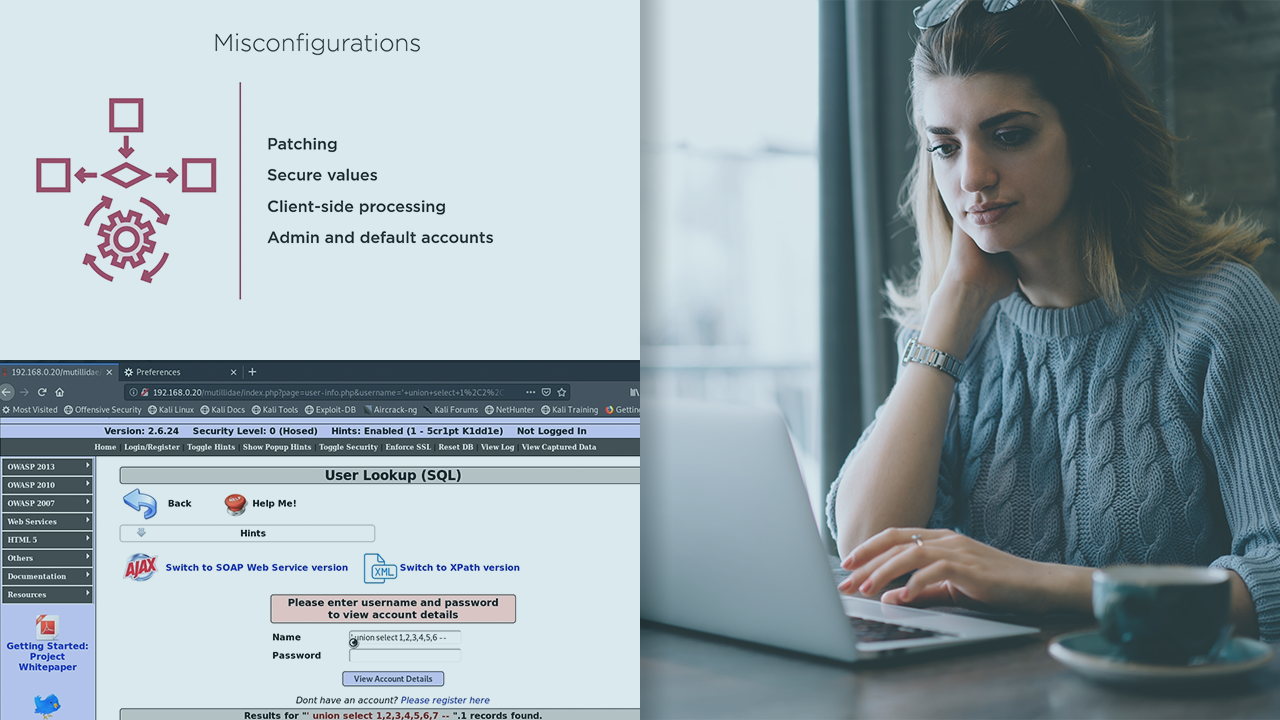
There are many different ways software can be flawed by both design and implementation, so you will need to accurately execute a wide variety of tests to assess each application that the business is responsible. In this course, Testing Applications for CompTIA PenTest+, you will learn how to exploit the vulnerabilities in web-based applications during an engagement. First, you will learn the commonalities among web-apps. Once you understand this, you will be able to utilize this knowledge to your advantage. Next, you will explore the different types of authentication, injection, and web shell attacks you can use to exploit these apps. Finally, you will use specific analysis techniques on compiled software to see if you can compromise these types of applications. When you are finished with this course, you will have the skills and knowledge of penetration tester needed to exploit most any app on any engagement.
Software required: [software required.] *
- Setting up the Lab environment from the "Laying the Foundation for Penetration Testing for CompTIA PenTest+" course.

