- Course
Wireshark Core Protocol Analysis
This course will enable you to use Wireshark to understand and analyze the network traffic going over your enterprise network.
- Course
Wireshark Core Protocol Analysis
This course will enable you to use Wireshark to understand and analyze the network traffic going over your enterprise network.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
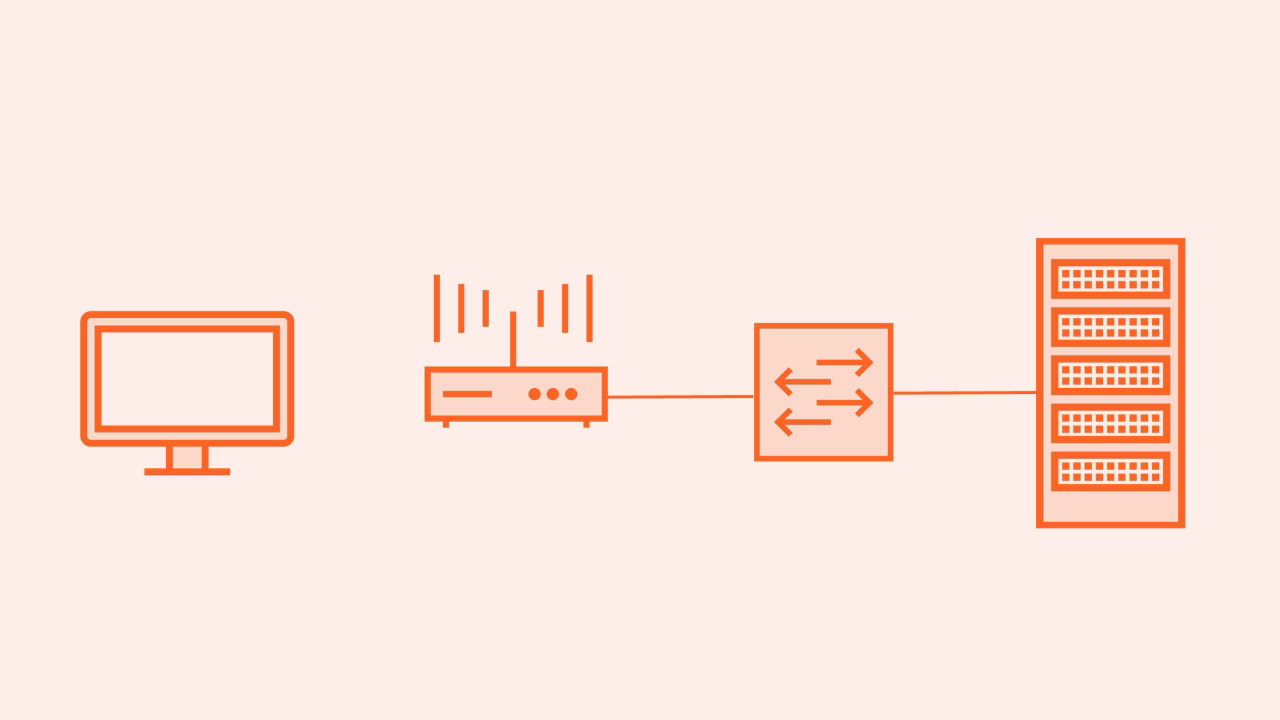
Wireshark is a network packet analysis tool that enables you to see the traffic going over the network. At the end of 2015, Wireshark 2.0 was released. This release radically changed the GUI, and added several major improvements. This course is based on this new version of Wireshark. It is recommended that you take the Wireshark 2.0 Fundamentals as a prerequisite to this course. In Wireshark Core Protocol Analysis, you will look at the key TCP/IP protocols used in today's enterprise networks. First, you'll learn about the four-step methodology for analyzing any network protocol. Next, you'll explore the eight most core protocols that are on today's enterprise networks. Finally, you'll wrap up the course by understanding key security protocols running on your network, and learn how to get yourself ready to support IoT on your enterprise network. By the end this course, you will have reinforced your understanding of how these eight core protocols work, be familiar with the key fields carried in the protocol header, and most importantly, you'll know what to look for when analyzing your enterprise (or even your home) network.

