- Course
Digital Forensics: Getting Started
Digital forensics is the process of recovery and investigation of digital artifacts involved in a cybercrime. This course will teach you the basics of evidence integrity, acquisition, examination, and analysis to finally create a forensics timeline.
- Course
Digital Forensics: Getting Started
Digital forensics is the process of recovery and investigation of digital artifacts involved in a cybercrime. This course will teach you the basics of evidence integrity, acquisition, examination, and analysis to finally create a forensics timeline.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
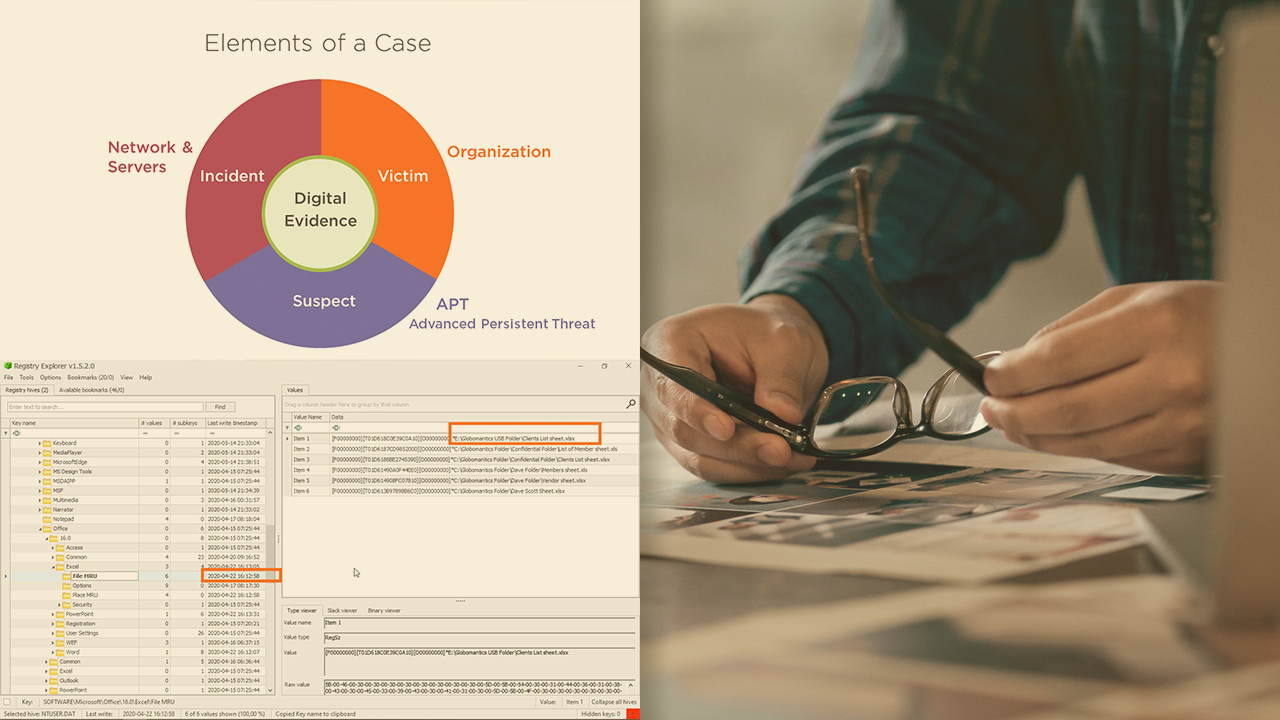
Digital forensics is now back in focus with the rapid increase in cybercrimes. In this course, Digital Forensics: Getting Started, you'll learn the skills required to conduct a digital forensics investigation from acquisition to the analysis phase. First, you'll discover the process of hypothesis testing by applying forensic science techniques to digital forensics. Next, you’ll explore how to overcome the challenges of digital evidence by using evidence integrity methods such as write blockers and verifying hashes. Finally, you'll learn how to examine the Windows Registry files and create a timeline of events for your case. When you’re finished with this course, you'll have a foundational understanding of the digital forensics domain that will help you conduct successful cybercrime investigations.

