- Course
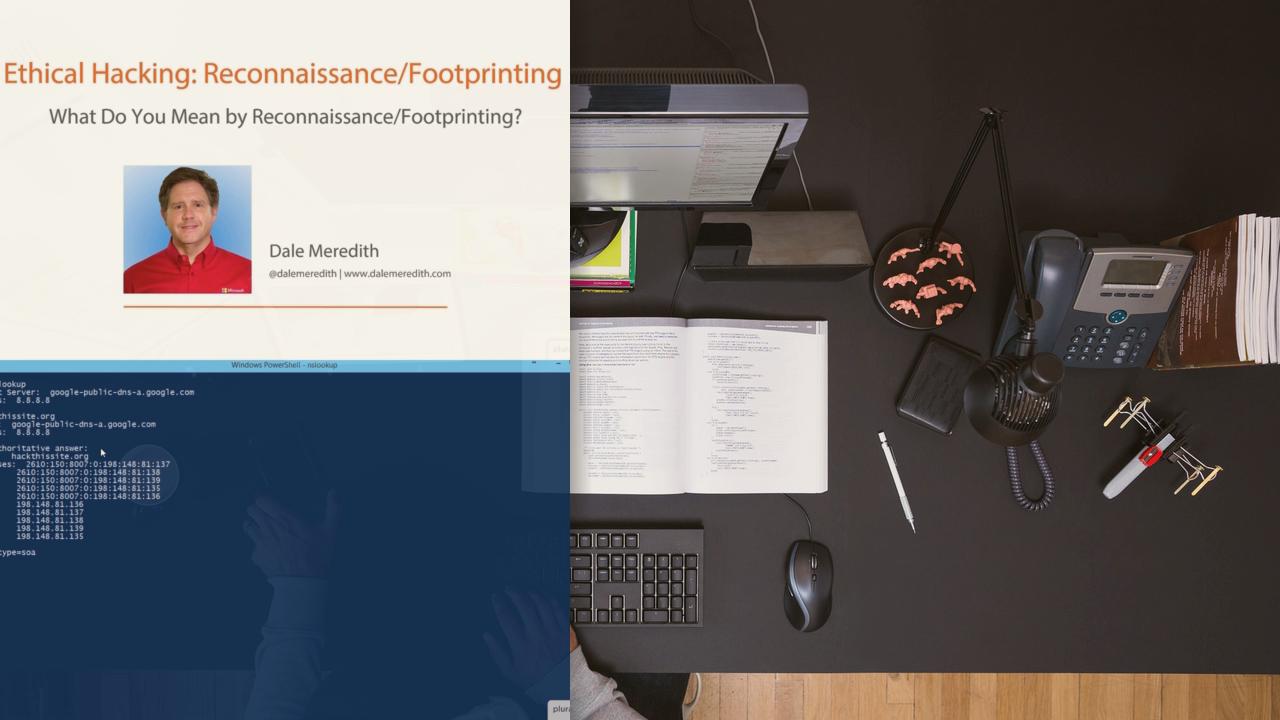
Ethical Hacking: Reconnaissance/Footprinting
Pluralsight is not an official partner or accredited training center of EC-Council. This course covers the process of probing a system with the intent of compromising the target. The goal is to gather as much data as possible about a would-be target.
- Course
Ethical Hacking: Reconnaissance/Footprinting
Pluralsight is not an official partner or accredited training center of EC-Council. This course covers the process of probing a system with the intent of compromising the target. The goal is to gather as much data as possible about a would-be target.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Pluralsight is not an official partner or accredited training center of EC-Council. As an Ethical Hacker, you've been asked to do a "Blackbox" attack on a customer's infrastructure. Your first step is finding out as much as you can about the "target." You accomplish this via reconnaissance/footprinting. This is the initial stage in gaining a blueprint of the security profile of a target, and it is accomplished in an organized manner. Reconnaissance is one of the three "pre-attack phases," and results in a unique profile of an organization's networks and systems. "Reconning" an organization is necessary in order to systematically gather all the related data in regards to the technologies deployed within the network. Reconnaissance can take up to 90% of the time during penetration testing or an actual attack. We'll show you how attackers are currently reconning your company, as well as discuss in detail the steps of reconnaissance. Finally we'll look at some possible countermeasures to help discourage attackers. This course is part of the Ethical Hacking Series. http://blog.pluralsight.com/learning-path-ethical-hacking

