- Course
Information Systems Asset Protection: Securing System Components
This course will provide you with the knowledge needed to audit the many different components that secure information systems. The IT auditor needs a diverse range of skills and expertise as addressed in this course to evaluate systems' security.
- Course
Information Systems Asset Protection: Securing System Components
This course will provide you with the knowledge needed to audit the many different components that secure information systems. The IT auditor needs a diverse range of skills and expertise as addressed in this course to evaluate systems' security.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
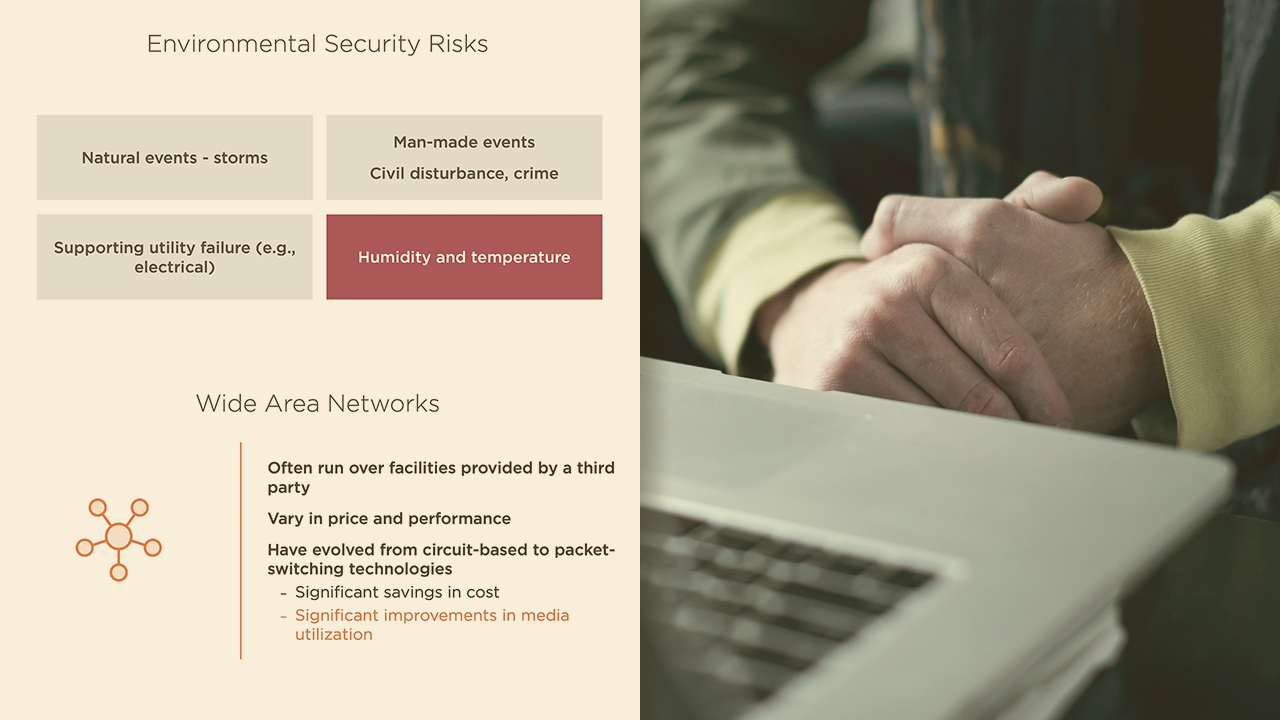
The IT auditor needs a diverse range of skills and expertise as addressed in this course to evaluate systems' security. In this course, Information Systems Asset Protection: Securing System Components, you will learn how to audit the security functionality of the many different components of information systems - ranging from networks and storage to end point devices and applications. This knowledge is essential for the auditor to be able to evaluate and report on the effective and secure operation of information systems. First, you will learn about identity and access management. Then, you will address network security. Finally, you will explore physical and environmental security and examining applications and virtual environments. When you are finished with this course, you will have the knowledge necessary to provide skilled audits of information systems' security.
Information Systems Asset Protection: Securing System Components
-
Identity and Access Management: Part One | 8m 4s
-
Identity and Access Management: Part Two | 9m 26s
-
Managing Logical Access: Part One | 8m 49s
-
Managing Logical Access: Part Two | 6m 42s
-
Managing Logical Access: Part Three | 5m 34s
-
Authorization and Accounting: Part One | 7m 9s
-
Authorization and Accounting: Part Two | 6m 7s
-
Authorization and Accounting: Part Three | 6m 58s

