- Course
Managing Splunk Enterprise Security Data and Dashboards
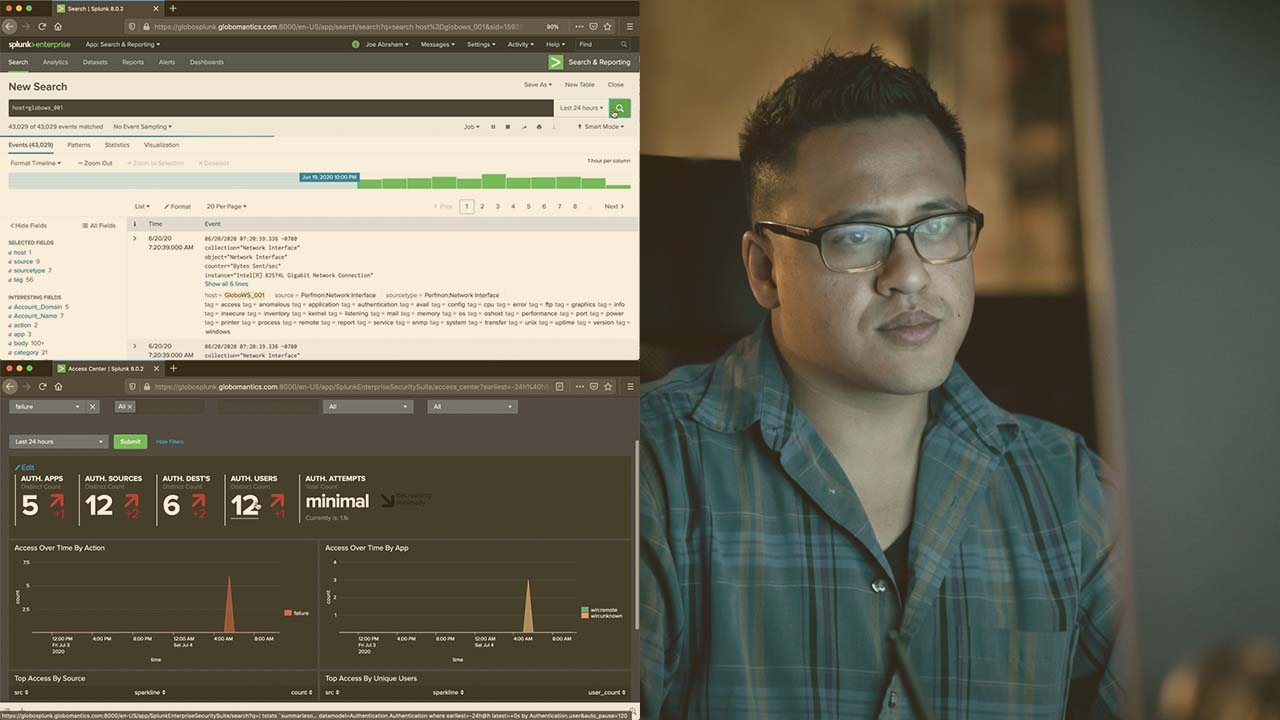
Splunk Enterprise Security is a premium application used within the Splunk deployment to help with SOC operations. This course will teach you how to manage your data, and manage the dashboards and feature using the data.
- Course
Managing Splunk Enterprise Security Data and Dashboards
Splunk Enterprise Security is a premium application used within the Splunk deployment to help with SOC operations. This course will teach you how to manage your data, and manage the dashboards and feature using the data.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Security
What you'll learn
Splunk Enterprise Security (ES) solves many problems within our SOCs, including efficient operations. In this course, Managing Splunk Enterprise Security Data and Dashboards, you’ll learn how to get the data usable for Splunk Enterprise Security and see how it can add to the function and uses of dashboards and features within the application. First, you’ll learn about the data ingestion and work through examples taking data and making it CIM-compatible for use for specific dashboards and features. Next, you’ll discover how to manage the dashboards that are available to you and how to modify them and the data to correspond to each other. Finally, you’ll learn how to configure and use features like the glass tables, forensics and investigation dashboards, and others. When you’re finished with this course, you’ll have the skills and knowledge of Splunk Enterprise Security needed to start ingesting data and administering it appropriately.

