- Course
Network Management and Operations
Networking hardware often fails, and requires policies, protocols, and monitoring to keep a data network in optimal shape. This course will teach you the policies and tools engineers use to keep networks up and running.
- Course
Network Management and Operations
Networking hardware often fails, and requires policies, protocols, and monitoring to keep a data network in optimal shape. This course will teach you the policies and tools engineers use to keep networks up and running.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
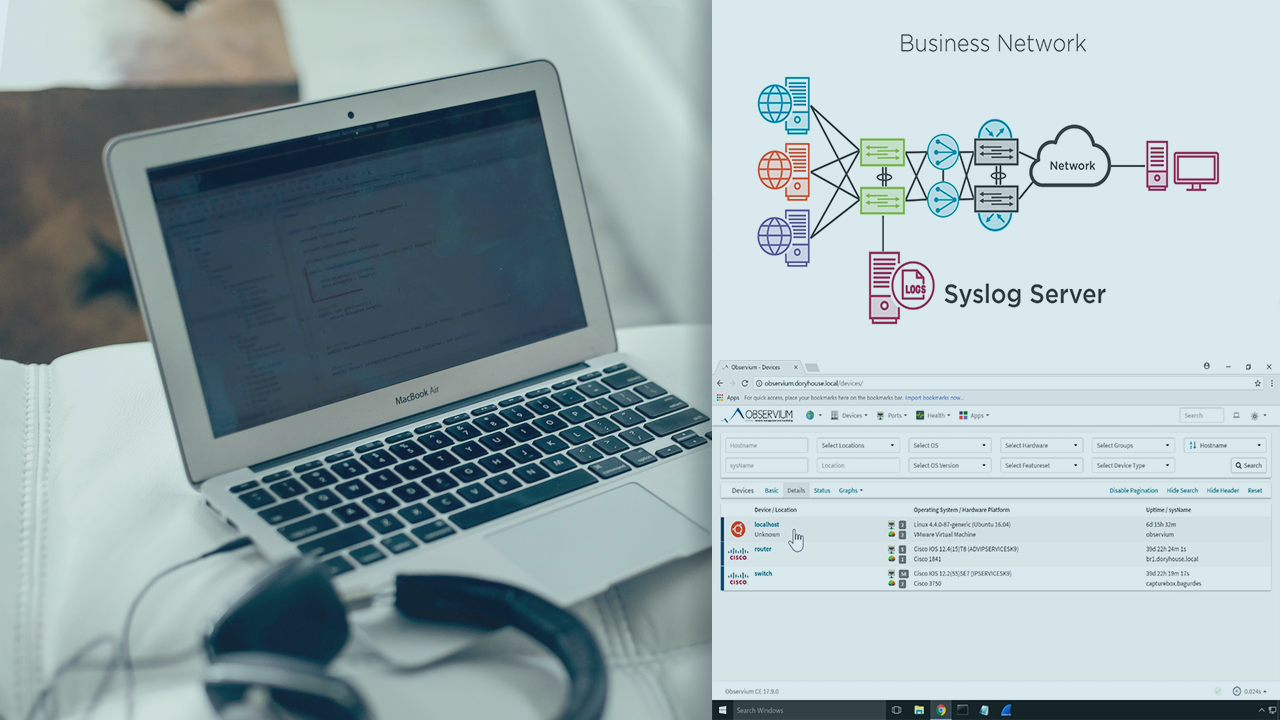
Understanding the vocabulary, protocol operation, and hardware configuration is surprisingly only a small component of maintaining an enterprise data network. In this course, Network Management and Operations, you will learn how data moves through systems and how to reliably and securely keep the network moving data. First, you will learn about different types of network documentation. Next, you will learn about the mechanisms that keep systems working, even when a device fails. Finally, you will explore the tools used to monitor the state of network devices. By the end of this course, you will understand the secure mechanism engineers use to access network hardware, as well as, understand the difference between a hot, cold, and warm data center site.

