- Course
RHEL 8: Managing Security
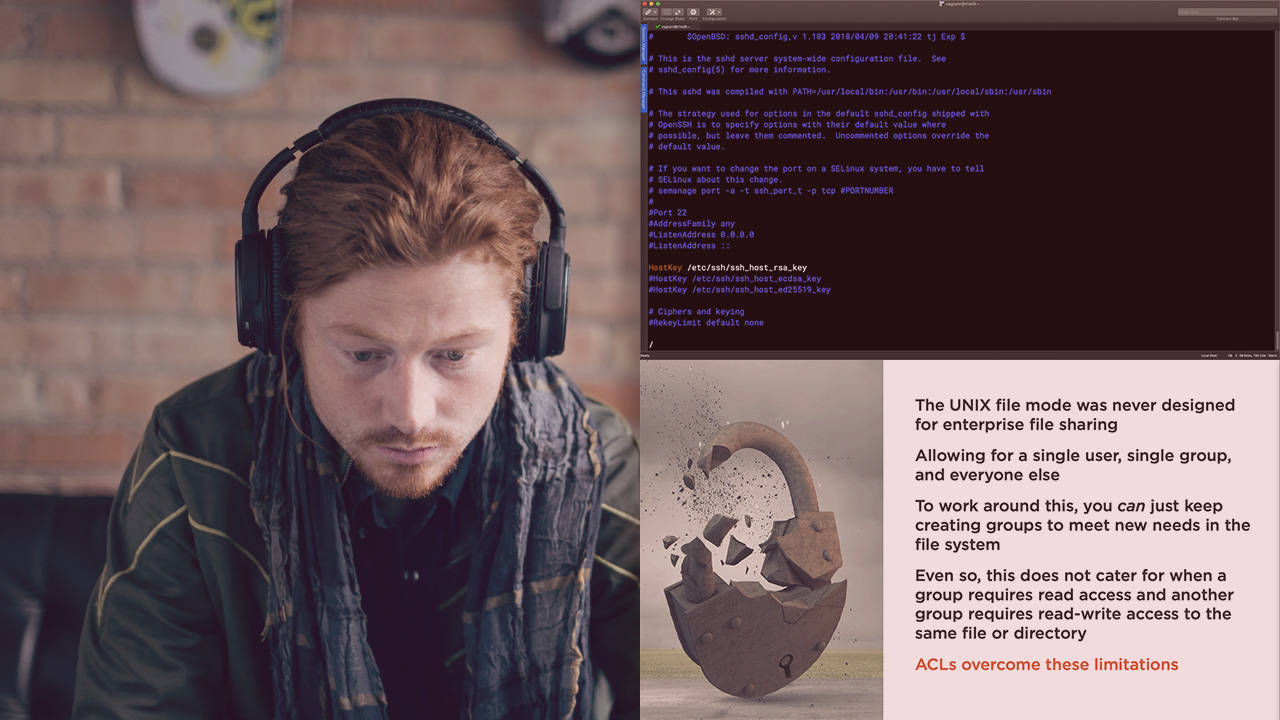
Security in Linux has never been so important. This course will teach you the skills needed to implement Mandatory Access Control Lists (SELinux) and key-based authentication.
- Course
RHEL 8: Managing Security
Security in Linux has never been so important. This course will teach you the skills needed to implement Mandatory Access Control Lists (SELinux) and key-based authentication.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
Keeping your data secure and your systems protected in now a legal requirement in most nations. In this course, RHEL 8: Managing Security, you’ll learn to develop a mindset to keep your systems secure. First, you’ll explore implementing key-based authentication to disable password access via SSH. Next, you’ll discover the reasons why SELinux is required and should never be disabled. Finally, you’ll learn how to implement SELinux policies to secure your system making adjustments for custom locations. When you’re finished with this course, you’ll have the skills and knowledge of securing Red Hat Enterprise Linux 8 needed to deploy systems in a public facing environment.

