- Course
Securing and Monitoring AWS Workloads
This course will teach you the various security services and strategies offered by AWS for securing your systems and complying with industry standards.
- Course
Securing and Monitoring AWS Workloads
This course will teach you the various security services and strategies offered by AWS for securing your systems and complying with industry standards.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Cloud
- Security
What you'll learn
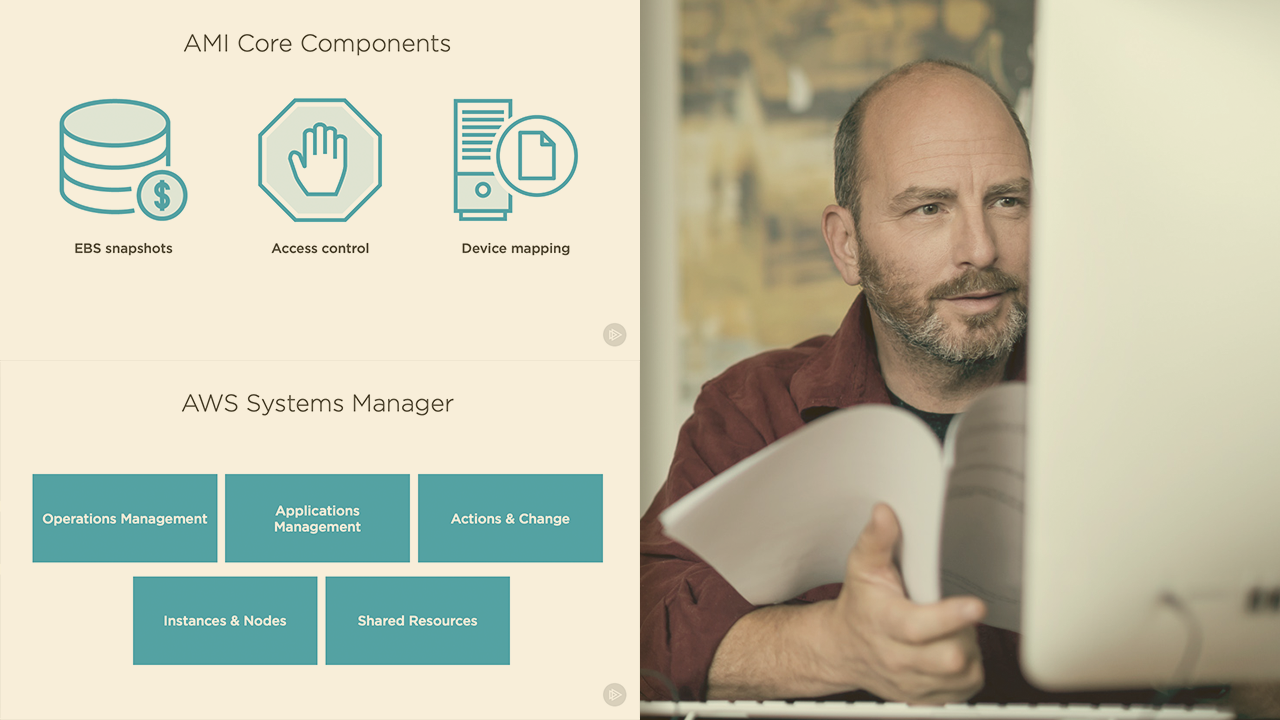
AWS has a plethora of services that caters to securing, monitoring, and alerting your environment and infrastructure. In this course, Securing and Monitoring AWS Workloads, you’ll learn to choose the right AWS services for the problem at hand and explore how to monitor and alert security violations and network compliance issues. First, you’ll explore the concept of hardening an AMI and the benefits of using hardened AMI, while launching an EC2 instance, perform security assessments on a hardened AMI using Amazon Inspector. Next, you’ll discover the importance of EC2 key pairs, the do’s and don’ts in managing the key pair, and how to use AWS Systems Manager to maintain a large number of EC2 instances effectively. Then, you will explore AWS Trusted Advisor, the services that are reserved for enterprise customers, and the services that are offered to all customers, and how to find security violations and implement solutions recommended by AWS. Finally, you’ll learn about AWS inspector and AWS Config, the default config rules provided by AWS, build custom rules, build an assessment template and run a security assessment, and check the findings. When you’re finished with this course, you’ll have the skills and knowledge of securing your EC2 instances, your environment, and the infrastructure that it is a part of setup monitoring and alerting solutions needed to build a highly secured AWS cloud application. You will also be prepared to clear your AWS advanced security specialty certification exam.


