- Course
Building a Cisco VCS Control Dial Plan and Expressway Remote Access Solution
Firewall traversal, secure remote access, and video endpoint registration are essential components in a multi-site Unified Collaboration deployment. This course will teach you how to configure Cisco VCS Control and VCS Expressway servers.
- Course
Building a Cisco VCS Control Dial Plan and Expressway Remote Access Solution
Firewall traversal, secure remote access, and video endpoint registration are essential components in a multi-site Unified Collaboration deployment. This course will teach you how to configure Cisco VCS Control and VCS Expressway servers.
Get started today
Access this course and other top-rated tech content with one of our business plans.
Try this course for free
Access this course and other top-rated tech content with one of our individual plans.
This course is included in the libraries shown below:
- Core Tech
What you'll learn
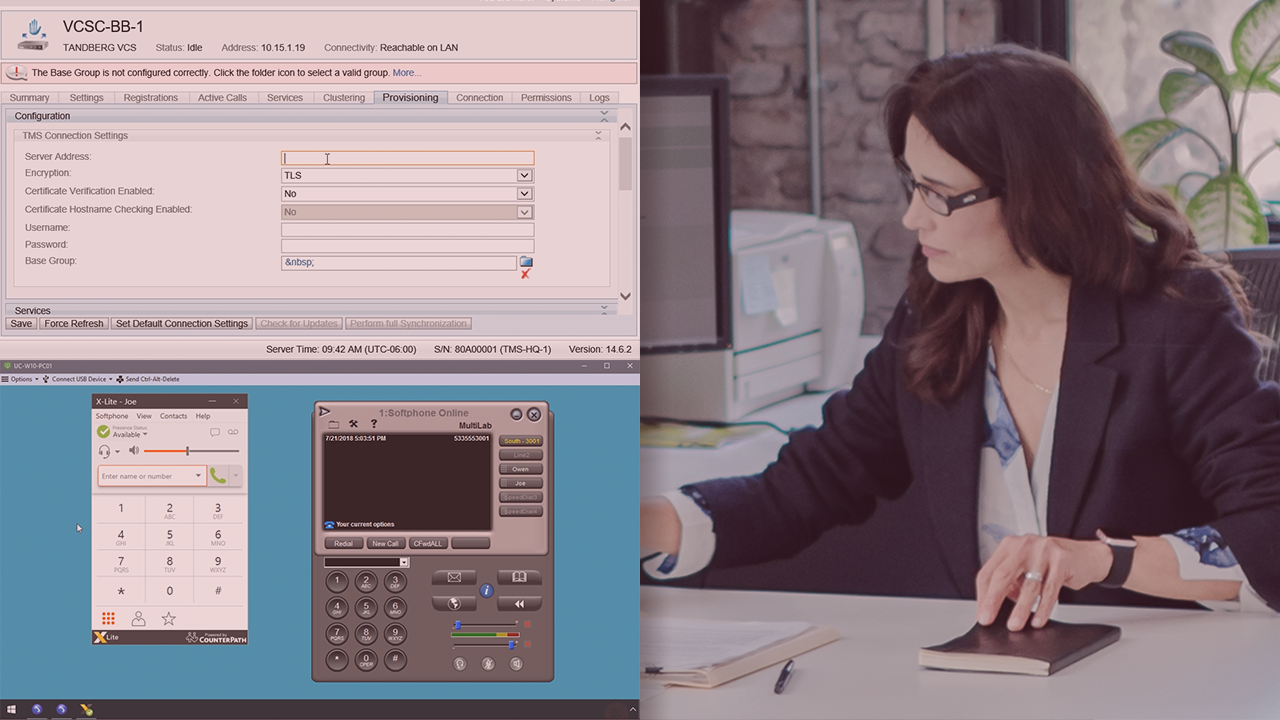
In today’s fast-paced world, the ability to communicate using real-time IP voice and video technology is a business necessity. In this course, Building a Cisco VCS Control Dial Plan and Expressway Remote Access Solution, you will learn the step by step process of registering SIP endpoints using a TelePresence VCS Control solution, as well as learn how to configure VCS Expressway to provide firewall traversal and secure remote access that doesn’t require a VPN. First, you will learn how to do the initial configuration of a Cisco VCS Control server and use TelePresence Management Server (TMS) to register users and SIP endpoints. Next, you will see how to configure Cisco Unified Communications Manager and Cisco VCS Control to communicate using SIP trunks, and configure Cisco VCS Expressway to provide edge services such as firewall traversal, business to business communications, and secure remote access. Then, you will explore how to configure DNS servers to support Jabber registration through the corporate firewall using Expressway-Edge and Core servers. Finally, you will review how to troubleshoot a variety of common “real world” configuration issues that can come up when building the features covered in this course. When you’re finished with this course, you’ll have the skills and knowledge needed to configure Cisco VCS Control and Expressway servers.

